Introduction 👋🏽
In this post, You will learn what is amass and how to use it and below is the video format of the post, Check it out 👇🏾
Video 📹
What is Amass❓
The OWASP Amass Project performs network mapping of attack surfaces and external asset discovery using open source information gathering and active reconnaissance techniques.
In simple amass is an information gathering tool, Which does the subdomain enum, information gathering and much more.
The tool uses third-party data’s to narrow down the user results. Below I have given what all the third-party the amass tool has partnership with ????????

Advertisement
Who Developed Amass Tool 🤔
The Amass was written by the OWASP leader jeff foley also know as caffix, Great tool mate ❤️, Below are the official links for amass kindly take a look at it 👇🏾
Installation ⬇️
Male sure you have installed, Go lang and amass dependencies.
Win: go install -v github.com/owasp-amass/amass/v3/…@master Linux: go install -v github.com/owasp-amass/amass/v3/...@master
Amass Feature 💡
The amass tool has some unique features such as;
- amass intel – Discover targets for enumerations
- amass enum – Perform enumerations and network mapping
- amass viz – Visualize enumeration results
- amass track – Track differences between enumerations
- amass db – Manipulate the Amass graph database
Each of they above are unique commands and gives unique results.
Advertisement
How to Use Amass ????
I have separated how to use amass in sub category, So we will be looking at ????????
- amass intel
- amass enum
- amass viz
- amass track
- amass db
Amass Intel
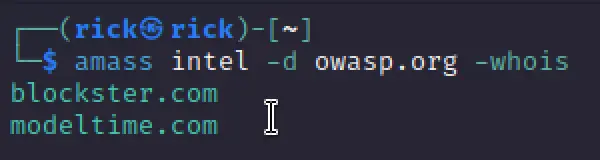
The amass intel gathers basic information against the target using various other tools, It find IPv4 IPv6 addr and basic whois informations.
amass intel -d owasp.org -whois
Using Amass, you have the option to search for organizational names.
This search can yield ASN IDs that have been assigned to the target. An illustrative example is provided below:
We can also scan a target just with a string, Take a look at the below example.
amass intel -org 'google'
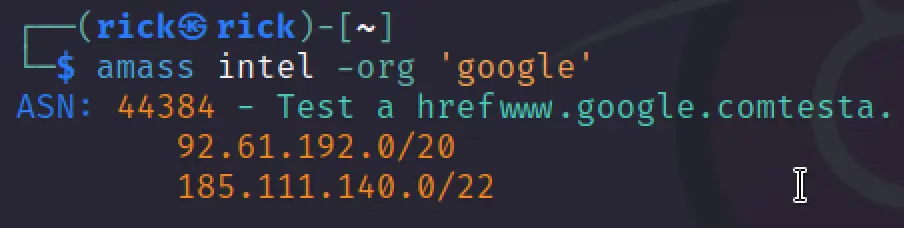
We can see that we have retrieved asn numbers, Let’s try using the asn id against the target.
amass intel -active -asn 44384 -ip
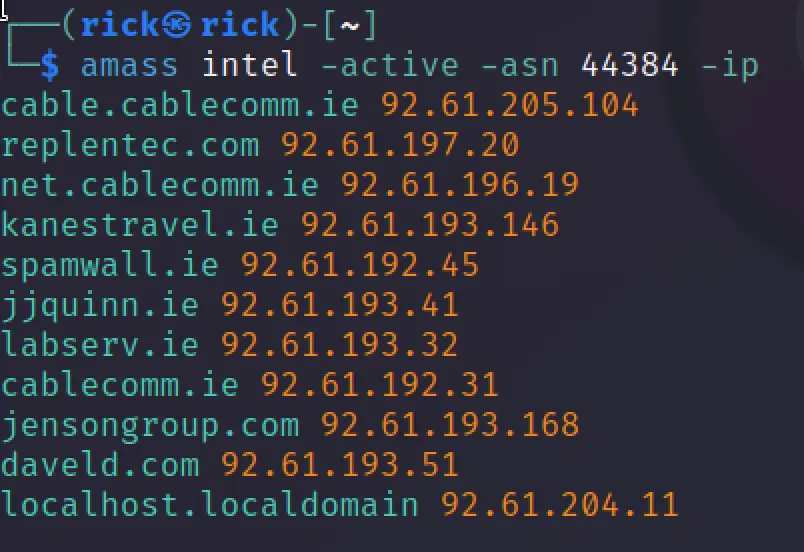
Here the -active mean it choose the way it want to scan the target. It can be the google index or webmaster index and much more.
In the above scan result we can see the subdomain associated with the asn id and also we can see the IPv4 addr.
Amass Enum
The enum option in amass will enumerate DNS services and also mapping around the network.
Take a good look at the below example.
amass enum -passive -d google.com -src

We can see that from the above results it has found the subdomains and also can see where the results has been came from, For example Anubis DB here…
We can also brute force the subdomains and try to get in, Let’s see how to do that ???? For EDUCATIONAL purpose only.
amass enum -active -d google.com -brute -w /usr/share/wordlists/amass/all.txt

Amass Track
The amass track helps to compare the results against the same target and narrow downs the results as we wish.
amass track -config /root/amass/config.ini -dir amass4owasp -d owasp.org -last 2
Amass Viz and Amass DB
Executing the command below will generate a complete inventory of enumerations conducted within the specified domains and stored in the “amass4owasp” graph database ????????
amass db -dir amass4owasp -list amass db -dir amass4owasp -d owasp.org -enum 1 -show
By utilizing the Amass viz subcommand, you gain the ability to visualize the accumulated information from a target in various formats, all of which are stored within the Amass graph database.
Furthermore, these results can be seamlessly imported into Maltego for in-depth analysis using OSINT (Open-Source Intelligence) techniques.
amass viz -d3 -dir amass4owasp

Conclusion
In my opinion I thought amass is just an another information gathering tool but amass is quiet great than I expected. It has got the feature the Maltego got but still amass is great.
Advertisement