Introduction
In this post, You will learn what is unicorn scan and how to use the tool and there will be a justification on the unicorn scan is faster than Nmap and masscan.
Below is the video format of the post, Check it out
Video
<What is Unicornscan ❓
Unicornscan is a new information gathering and correlation engine built for and by members of the security research and testing communities.
It was designed to provide an engine that is Scalable, Accurate, Flexible, and Efficient.
Basically the unicorn scan goes under the network mapping category.
In My personal experience unicornscan is faster than any of the network mapping tools, The tool is especially faster when you do an open port scan.
Advertisement
How to install unicornscan
In kali and Debian machines just do a sudo apt-get update and then enter sudo apt-get install unicornscan
Click the below download button to install the tool
How to use unicornscan
It is pretty much very easy to use the tool but the commands are difficult to remember. Ok, Let’s start our unicornscan tutorial.
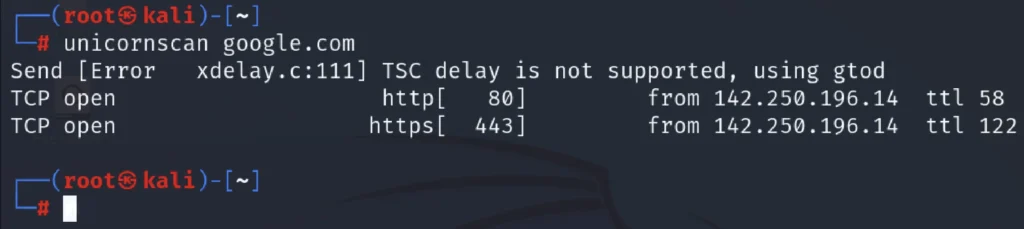
Default scan
To the default scan just enter unicornscan and the domain name, The syntax will be something like this unicornscan <domain name or IP>
unicornscan google.com
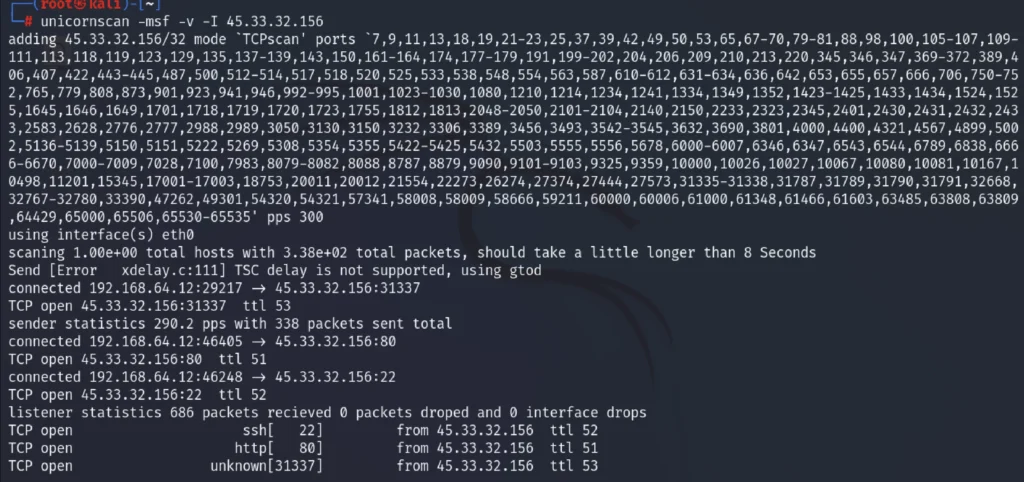
TCP SYN Scan
We are performing TCP SYN scan on an whole network, All the live host will be seen from this command and we could also see the service and open port available.
unicornscan -msf -v -I 45.33.32.156
UDP Scan
Let’s perform an UDP scan.
unicornscan –mU –v –I 192.168.1.1/24

Open and Closed port scan
To scan for open and closed port just enter the below command
unicornscan -r30 -mT adaptercart.com

Scanning Multiple host
To scan for multiple host just enter the host IP or domain name by giving a space.
unicornscan google.com techyrick.com

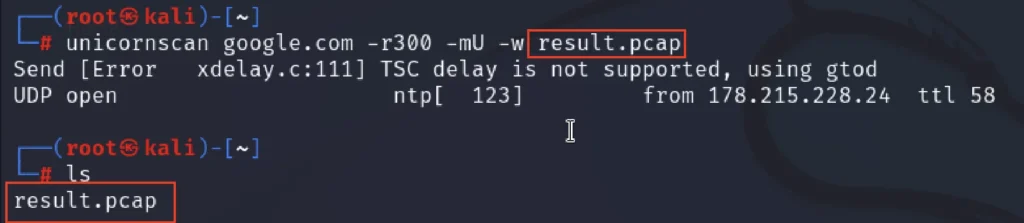
Save result in .pcap
Saving the result in .pcap and importing the .pcap file on Wireshark or Tshark gives more information about the protocols and the OSI models.
Advertisement
To save the result in .pcap just enter -w command,
unicornscan -r300 -mU 192.168.112.57 -w udpports.pcap
Conclusion
This is the best and fast tool for network mapping and there are only few options, Where we can’t easily identify the OS & Version of the target.
In my personal life I use this tool to just scan for all open and closed ports.
Hope you like the blog post ????
Advertisement
Also Read: Nmap full tutorial
Also Read: Masscan Tutorial