Introduction
In this post, you will learn how to browse Anonymously and I consider this post is very Important than other posts because this is about your privacy. So, please share the post with your friends and family to stay private.
And also, If you knew something about searching Anonymously, please comment down below.
Video
How to Browse Anonymously
Seems that you’re coming here after browsing on the Dark web, just kidding. Just browsing on incognito is not safer, maybe you’re not doing any illegal activities. But many will be after your personal information so, to keep your identity safer, you should browse anonymously.
Staying private online is not very much difficult and everyone can do it.
Let’s go with some easy strategies to browse anonymously.
VPN
Starting from our favourite one, VPN Stands for “Virtual private network” and I have already explained what is a VPN and how it works exactly [Click here] to read that post.
For those who are new to VPN, I’m going to explain very shortly. When you turn on VPN and search for something, usually all the searches will go to your ISP but the VPN redirects to their server so, no one can find and some VPN has got no logging system that means it auto deletes the information they get in the server. VPN Generally encrypts your data by changing their location from one country server to another. Take a look at the below image to analyze how a VPN encrypts your data.
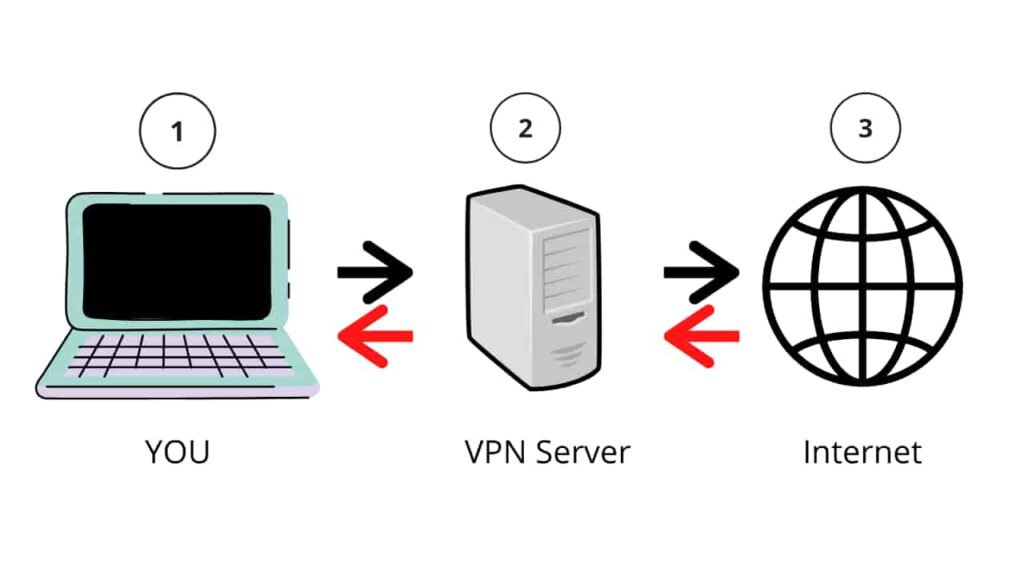
From the above image, we could easily understand whatever you search on Internet the search goes through a VPN server in an encrypted format and goes to the destination.
The VPN is just one tool to keep your data safe. We can assure VPN can block unnecessary Ads and firewalls.
Onion router or TOR
The second-best method to stay anonymous is Onion routers or TOR. These are not physical routers. Onion router or TOR is an Internet networking protocol that is integrated with the TOR browser. The TOR by default designed to stay Anonymous. The TOR browser creates multiple encryptions through their servers so, it is really very difficult to track you down. Take a look at the below image of how TOR Works.

The TOR browser creates multiple nodes and then finally goes to the destination. When you use TOR it is really very impossible to check your webmail, activities or search history.
TOR is also imperfect because they have got an exit node through that we could take lots of personal information so, that is why we use VPN over Tor. But if you are using it for casual surveillance then TOR itself is more than enough.
In conclusion, I can say Incognito, VPN and TOR are more than enough for a common person, but in this post, we are going for ultimate private browsing. Let’s see how.
Tails – Browse Anonymously
Linux based tails are designed to browse anonymously, and it is also designed in a way that it forgets all the data it sees. Not only the browser network runs around the tails also all other Network in your computer goes through Tails. Once you turn off your device, all the data will be lost and none of the identity will match with browsing history.
After installing Tails in your device.
And then disable your JavaScript and download a browser extension called privacy badger to stop Ad blocks, and finally set your default search engine to duck duck go.
And now you can browse Anonymously, Where no one can identify you. There is also one disadvantage that is speed. When you search for something, the information goes through multiple nodes. So, the speed of the search will automatically decrease and nothing we can do about it if you want to search Anonymously.
Conclusion
In conclusion, I suggest everyone use Incognito, VPN and TOR for just Casual surveillance and for Advanced Private browsing use tails.