Introduction
In this post, you will learn about 9 Popular Ransomware attacks in real life and If you knew something about ransomware, leave a comment below. I have already written a post on what is Ransomware to read [Click here].
Top 9 Ransomware Attacks
Locky
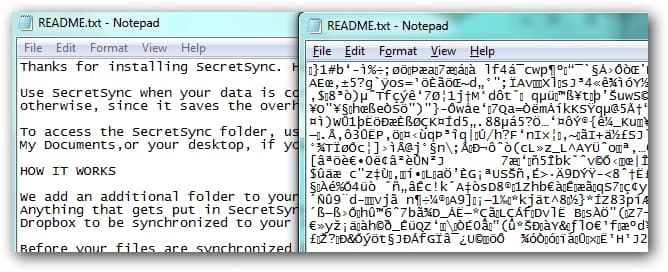
Locky is a Ransomware attack. This is one of the first attacks of 2016, and it is an organized cyberattack. This particular ransomware malware was spread through Word doc, which contains malicious macros. This attack was spreader through spam mails. Therefore, This attack was taking place because of untrained employees.
Once the user clicks on the doc, then it says “Enable macro if data encoding is correct”. Now the user clicks on the link, then it starts to encrypt the files which match the extensions.
Source: https://en.wikipedia.org/wiki/Locky
And then ask the user to download TOR and go to an instruction link page, and the link asked for 1 bitcoin to decrypt the files.
Also Read: What is a cryptographic key?
Wanna cry
Wanna cry would be one of the biggest ransomware attacks in history. This attack was firstly found in 2017 and spread almost to 150 countries. The malware was designed to exploit the security vulnerability in widows, which was created by NSA and the cybercrime group did this attack is named shadow broker.
Shadow Brokers hacking group presence was very active before this attack. According to Kaspersky. More than 2lakh computers were affected because of wanna cry ransomware.

Source: https://en.wikipedia.org/wiki/WannaCry_ransomware_attack
The shadow brokers or Lazarus group encrypted files and demanded for ransom in bitcoins. In this attack, mostly the cybercriminals targeted hospitals. 92 million pounds would be pay to the hackers from only the hospital attacks. The wanna cry approximate worldwide damage cost was 4 Billion.
Also Read: How forget password works
Bad Rabbit – Ransomware attack
Bad Rabbit ransomware attack also took place in the year 2017, This ransomware attack spread through drive-by attacks. Cybercriminals injecting malicious software into a site. And users visit the site, they would be infiltrated by malware. This ransomware installs fake Adobe flash and does the attacks.

Ryuk – Ransomware attack
This ransomware attack was first noticed in Aug 2018. And the first suspect here is a North Korean organization. And it is suspected of two or more Russian criminal organizations have done the attack. Most of the attack was towards business and schools. This ransomware attacks would seem to be a personal or targeted attack, the hacker group just want the ransom.
Also Read: What is a computer worm? How computer worms work
Shade or Troldesh
Shade or Troldesh ransomware attack first noticed in 2015. And this malware was spreader through phishing. The favourite part here, the Troldesh hacker group communicated directly to victims. And who is cooperating to the organization they gave a discount.
Also Read: What is a computer virus and how it works?
Jig Shaw
Jig Shaw was a ransomware attack. The name jig Shaw kept after a movie name. This attack found at 2016. And these cybercriminals deleted each file for unpaid ransom for every hour. In addition, the visuals were very frightening. This is also one of the dangerous ransomware attacks.

Source: https://en.wikipedia.org/wiki/Jigsaw_(ransomware)
CryptoLocker – Ransomware attack
It is one of the oldest ransomware attacks, which found in 2007 and the malware spreader through phishing attacks. This ransomware encrypted 5lakh computers and law enforcement seized a worldwide network of encrypted computers.

As a result, when the user clicks, it redirects to an online portal and demands for crypto to unlock the portal.
Petya ransomware attack
Petya attack, founded in 2016 and this malware encrypts full hard disk. Did by encrypting the Master file table (MFT). This ransomware spread through fake applications that contain a malicious link. Another updated variant is Petya 2.0 or also called GoldenEye.
Golden Eye
This GoldenEye ransomware was first found in 2017 and also called Wanna cry’s sibling. This attack targeted banks and several pipelines. And more than 2000 systems are encrypted during this attack.
Also Read: What is Trojan? How it works!
Also Read: What is Ransomware?
Read: What is spyware exactly? How spyware works and different types of spyware