Introduction
worm attack: In this post, you will learn about Top 3 worm attacks in real life. And I have already written a post on what is Computer worm and how it works and its types to read[click here].
Top 3 Worm Attacks in real life
Let’s see a small recap on what is a computer worm? A computer worm is a type of Malware, which is created by cybercriminals to harm a user computer. Computer worm stands for “Write Once, Read Many“. A Computer worm can duplicate itself and can spread to connected devices. These computer worms don’t need any human’s interaction to execute.
Morris Worm – 1988, worm attack
This is the first worm attack, which is available on the record. The developer of this Morris worm is Rober Tappen Morris Jr. He is a kernel graduated student. So, Let’s see how this worm has attacked 60k systems.
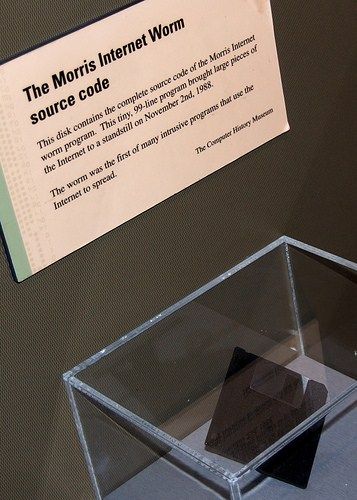
Firstly, the malware is put on ARPANET, ARPANET is the basis for the Internet and the system connected to the network was also infected, More than 60K Systems were infected and the attack repeatedly took place on the same computers. And cybersecurity experts say this is the first DOS attack on record.
Also Read: Top 3 Computer Virus Attacks in real-world
I LOVE YOU Worm – 2000, worm attack

If you have read my previous post, you would know that I have brought I LOVE YOU Malware in the subset of Virus and still here I bring the same malware in the Worm subset. Why?
First;y, The I LOVE YOU Malware is a trojan that carried Worms and Virus Malware. The Malware showed both Virus and Worm characteristics so, I have added this attack in the worm subset.
The I LOVE YOU Malware was spread via spam E-Mails and the text was in a Pdf format. The message written in the Pdf is a romantic love letter along with malicious codes. Public people shared the malware because the letter triggered them.
The Malware affected more than a 45Million user’s computers and the pentagon and Ford motors E-mails were temporarily shut down.
Also Read: Top 3 Trojan Attacks in real-world
Stuxnet – 2010, worm attack
Stuxnet is a type of Virus and also worm. This malware did both Virus and worm attacks, This malware was firstly noticed in the year 2010, and lost its scope and got an upgrade from the developer of Malware in the year 2015.
This a government-sponsored attack the primary target here is to terminate Iran Nuclear program.
Also Read: Top 5 Spyware attacks in real-world
Also Read: Top 3 Rootkit attacks in real world