Introduction
In this post, you will learn what is SQL injection and in addition, I will explain how website hacking became more popular and at last you will learn if the SQL based languages are really effective!!!
Hey, wait I thought of adding cross-site scripting also to post. So, after reading this post you will have a basic knowledge about SQL and cross-site scripting.
Also Read: Hiren’s boot cd and Linux cd overview
How website compromising became popular?
Back in the 90’s hacking a website was fun but now it isn’t most of the sensitive data’s are on the websites and in the 90’s all the military and government information was offline. But now most of the military and Government sensitive data are in the cloud. And the hackers try each and every day to take the sensitive information and sell it to the next country or a third party.
When I say sensitive information, The information can be an activation code for nuclear weapons. Maybe the targeted persons NSFW pics or videos and hackers found these kinds of videos and pics. Surely demand a massive ransom.
Most of the schools, organisations, Top companies, Governments and everyone are having their own domain and website. There are tons of sensitive information and hacker will be ready to steal them at any point.
There are many ways a website can be compromised. I recommend that take a look at the Top 10 OWASP (Open Web Application Security Project) Projects.
Back in the ’90s, there were no tools such as but with, the harvester, sublist3r, we leak info. to. These are the tools that are used to gather information about a particular website.
According to my knowledge still, website hacking is very much popular but SQL injection and cross-site scripting became a little old and there are various other new methods to compromise a website.
Also Read: What is on-boot?
What is SQL injection?
Firstly, SQL stands for “structure query language“. SQL injection is a code injection attack, yes this attack can be only performed against the websites. The attack can take place in SQL or PHP language and these attacks are very traditional but still many websites are having old versions and untrained employees are the reasons for SQL injection attacks.
How do SQL attacks work?
SQL and PHP attacks are really very case sensitive and the hacker should firstly enter the codes into an executable format. Which either the hacker should physically or through anyways he/she should enter the code into the site.
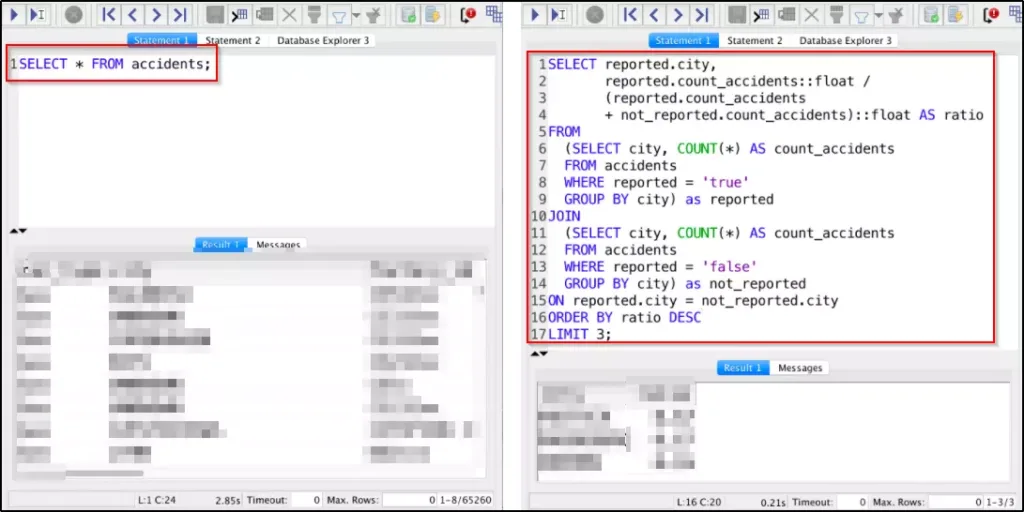
In order to create a valid SQL and PHP attack, a hacker should create a valid SQL or PHP script. Let’s see an example of SQL
Example: “or = “1” =”1 and ” or “a” = “a
As you could see the above script is incomplete but it fools the SQL language script. The hacker should enter the code in the login page and once the original user login then for sure the username and the password is will be captured by the hacker.
What is cross-site scripting?
The cross-site scripting is the same as the SQL injection attack but the language users here is javascript. I don’t see the cross-site scripting is very much effective because most of the sites are made of PHP language.
Apart from SQL, cross-site scripting is executed dynamically in the front or the backend of the websites. Most of the XSS scripting is done to get cookies and caches and also the alert box of the site.
There is also stored XSS scripting which is used for spying on the site the script is injected inside the database of the site and kept in an HTML format and the code will execute every time the user login to the particular site.
I recommend you to check this page for further information “Excess XSS“. Just enter the site and read full the information about XSS scripting.
Also Read: How IoT is involved in cyberattacks?
Also Read: What is external and internal recon